|
Lattice-based Access Control
In computer security, lattice-based access control (LBAC) is a complex access control model based on the interaction between any combination of objects (such as resources, computers, and applications) and subjects (such as individuals, groups or organizations). In this type of label-based mandatory access control model, a lattice is used to define the levels of security that an object may have and that a subject may have access to. The subject is only allowed to access an object if the security level of the subject is greater than or equal to that of the object. Mathematically, the security level access may also be expressed in terms of the lattice (a partial order set) where each object and subject have a greatest lower bound (meet) and least upper bound (join) of access rights. For example, if two subjects ''A'' and ''B'' need access to an object, the security level is defined as the meet of the levels of ''A'' and ''B''. In another example, if two objects ''X'' and ''Y'' ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, theft of, or damage to hardware, software, or data, as well as from the disruption or misdirection of the services they provide. The field has become of significance due to the expanded reliance on computer systems, the Internet, and wireless network standards such as Bluetooth and Wi-Fi, and due to the growth of smart devices, including smartphones, televisions, and the various devices that constitute the Internet of things (IoT). Cybersecurity is one of the most significant challenges of the contemporary world, due to both the complexity of information systems and the societies they support. Security is of especially high importance for systems that govern large-scale systems with far-reaching physical effects, such as power distribu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Discretionary Access Control
In computer security, discretionary access control (DAC) is a type of access control In the fields of physical security and information security, access control (AC) is the selective restriction of access to a place or other resource, while access management describes the process. The act of ''accessing'' may mean consuming ... defined by the Trusted Computer System Evaluation Criteria (TCSEC) as a means of restricting access to objects based on the identity of subjects and/or groups to which they belong. The controls are discretionary in the sense that a subject with a certain access permission is capable of passing that permission (perhaps indirectly) on to any other subject (unless restrained by mandatory access control). Discretionary access control is commonly discussed in contrast to mandatory access control (MAC). Occasionally, a system as a whole is said to have "discretionary" or "purely discretionary" access control when that system lacks mandatory access co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security Models
A computer is a machine that can be programmed to automatically carry out sequences of arithmetic or logical operations (computation). Modern digital electronic computers can perform generic sets of operations known as programs. These programs enable computers to perform a wide range of tasks. The term computer system may refer to a nominally complete computer that includes the hardware, operating system, software, and peripheral equipment needed and used for full operation; or to a group of computers that are linked and function together, such as a computer network or computer cluster. A broad range of industrial and consumer products use computers as control systems, including simple special-purpose devices like microwave ovens and remote controls, and factory devices like industrial robots. Computers are at the core of general-purpose devices such as personal computers and mobile devices such as smartphones. Computers power the Internet, which links billions of computers ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IEEE Computer
''Computer'' is an IEEE Computer Society practitioner-oriented magazine issued to all members of the society. It contains peer-reviewed articles, regular columns, and interviews on current computing-related issues. ''Computer'' provides information regarding current research developments, trends, best practices, and changes in the computing profession. Subscriptions of the magazine are provided free of cost to IEEE Computer Society members. ''Computer'' covers all aspects of computer science. Since 2009, it has a digital edition too. The current editor in chief (since 1 January 2020) is Jeff Voas of NIST. Its impact factor The impact factor (IF) or journal impact factor (JIF) of an academic journal is a scientometric index calculated by Clarivate that reflects the yearly mean number of citations of articles published in the last two years in a given journal, as ... was 1.94 for 2017, and 3.564 for 2018. The magazine is the recipient of the 2015 APEX Award for Publication Ex ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Communications Of The ACM
''Communications of the ACM'' is the monthly journal of the Association for Computing Machinery (ACM). It was established in 1958, with Saul Rosen as its first managing editor. It is sent to all ACM members. Articles are intended for readers with backgrounds in all areas of computer science and information systems. The focus is on the practical implications of advances in information technology and associated management issues; ACM also publishes a variety of more theoretical journals. The magazine straddles the boundary of a science magazine, trade magazine, and a scientific journal. While the content is subject to peer review, the articles published are often summaries of research that may also be published elsewhere. Material published must be accessible and relevant to a broad readership. From 1960 onward, ''CACM'' also published algorithms, expressed in ALGOL. The collection of algorithms later became known as the Collected Algorithms of the ACM. See also * ''Journal of the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
RSBAC
Rule-set-based access control (RSBAC) is an open source access control framework for current Linux kernels, which has been in stable production use since January 2000 (version 1.0.9a). Features * Free open source GNU General Public License (GPL) Linux kernel security extension * Independent of governments and big companies * Several well-known and new security models, e.g. mandatory access control ( MAC), access control list ( ACL), and role compatibility (RC) * On-access virus scanning with Dazuko interface * Detailed control over individual user and program network accesses * Fully access controlled kernel level user management * Any combination of security models possible * Easily extensible: write your own model for runtime registration * Support for latest kernels * Stable for production use * Easily portable to other operating systems The RSBAC system architecture has been derived and extended from the Generalized Framework for Access Control ( GFAC) by Marshall Abrams and L ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Role-based Access Control
In computer systems security, role-based access control (RBAC) or role-based security is an approach to restricting system access to authorized users. It is an approach to implement mandatory access control (MAC) or discretionary access control (DAC). Role-based access control is a policy-neutral access-control mechanism defined around roles and privileges. The components of RBAC such as role-permissions, user-role and role-role relationships make it simple to perform user assignments. A study by NIST has demonstrated that RBAC addresses many needs of commercial and government organizations. RBAC can be used to facilitate administration of security in large organizations with hundreds of users and thousands of permissions. Although RBAC is different from MAC and DAC access control frameworks, it can enforce these policies without any complication. Design Within an organization, roles are created for various job functions. The permissions to perform certain operations are ass ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Risk-based Authentication
In Authentication, risk-based authentication is a non-static authentication system which takes into account the profile (IP address, User-Agent HTTP header, time of access, and so on) of the agent requesting access to the system to determine the risk profile associated with that transaction. The risk profile is then used to determine the complexity of the challenge. Higher risk profiles leads to stronger challenges, whereas a static username/password may suffice for lower-risk profiles. Risk-based implementation allows the application to challenge the user for additional credentials only when the risk level is appropriate. The point is that user validation accuracy is improved without inconveniencing a user and risk-based authentication is used by major companies. Criticism * The system that computes the risk profile has to be diligently maintained and updated as new threats emerge. Improper configuration may lead to unauthorized access. * The user's connection profile (e.g. IP Geol ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Organisation-based Access Control
In computer security, organization-based access control (OrBAC) is an access control model first presented in 2003. The current approaches of the access control rest on the three entities (''subject'', ''action'', ''object'') to control the access the policy specifies that some subject has the permission to realize some action on some object. OrBAC allows the policy designer to define a security policy independently of the implementation. The chosen method to fulfill this goal is the introduction of an abstract level. * Subjects are abstracted into roles. A role is a set of subjects to which the same security rule apply. * Similarly, an activity is a set of actions to which the same security rule apply. * And, a view is a set of objects to which the same security rule apply. Each security policy is defined for and by an organization. Thus, the specification of the security policy is completely parameterized by the organization so that it is possible to handle simultaneously s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mandatory Access Control
In computer security, mandatory access control (MAC) refers to a type of access control by which the operating system or database constrains the ability of a ''subject'' or ''initiator'' to access or generally perform some sort of operation on an ''object'' or ''target''. In the case of operating systems, a subject is usually a process or thread; objects are constructs such as files, directories, TCP/ UDP ports, shared memory segments, IO devices, etc. Subjects and objects each have a set of security attributes. Whenever a subject attempts to access an object, an authorization rule enforced by the operating system kernel examines these security attributes and decides whether the access can take place. Any operation by any subject on any object is tested against the set of authorization rules (aka ''policy'') to determine if the operation is allowed. A database management system, in its access control mechanism, can also apply mandatory access control; in this case, the objects ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Location-based Authentication
Location-based authentication is a special procedure to prove an individual's identity on appearance simply by detecting its presence at a distinct location. To enable location-based authentication, a special combination of objects is required. * Firsthand, the individual that applies for being identified and authenticated has to present a sign of identity. * Secondly, the individual has to carry at least one human authentication factor that may be recognized on the distinct location. * Thirdly, the distinct location must be equipped with a resident means that is capable to determine the coincidence of individual at this distinct location. Distinctiveness of locating Basic requirement for safe location-based authentication is a well-defined separation of locations as well as an equally well-defined proximity of the applying individual to this location. Challenges , no offered technical solution for simple location-based authentication includes a method for limiting the gra ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Graph-based Access Control
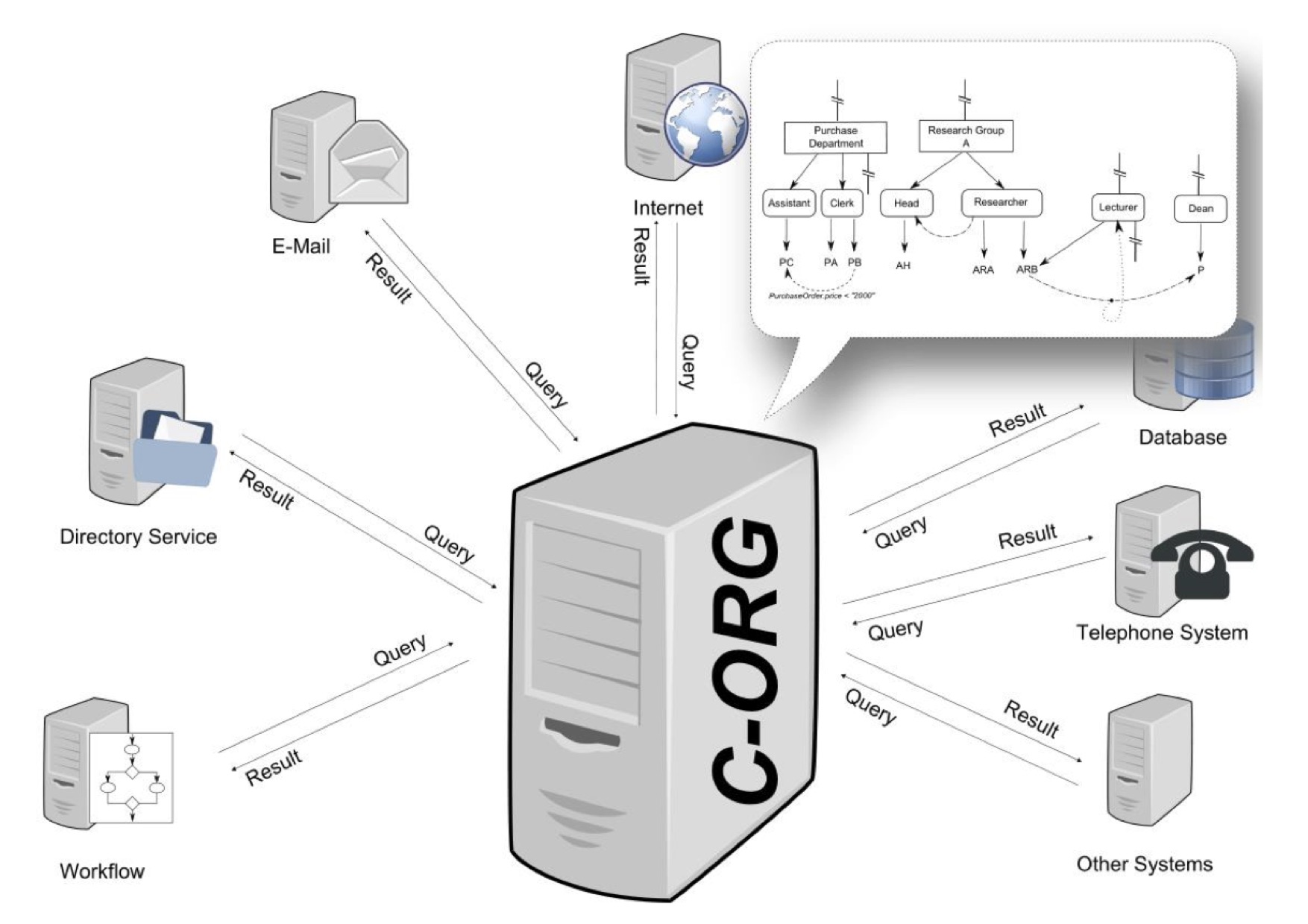
Graph-based access control (GBAC) is a declarative way to define access rights, task assignments, recipients and content in information systems. The access rights are granted to objects like files or documents, but also business objects like an account. It can also be used for the assignment of agents to tasks in workflow environments. Organizations are modeled as a specific kind of semantic graph comprising the organizational units, the roles and functions as well as the human and automatic agents (i.a. persons, machines). Compared to other approaches like role-based access control or attribute-based access control, the main difference is that in GBAC access rights are defined using an organizational query language instead of total enumeration. History The foundations of GBAC go back to a research project named CoCoSOrg (Configurable Cooperation System) ">ref name = DISS>(in English language please see ) at Bamberg University. In CoCoSOrg an organization is represented as a se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |