|
Kleptographic Attack
Kleptography is the study of stealing information securely and subliminally. The term was introduced by Adam Young and Moti Yung in the Proceedings of Advances in Cryptology—Crypto '96.A. Young, M. Yung, "The Dark Side of Black-Box Cryptography, or: Should we trust Capstone?" In Proceedings of Crypto '96, Neal Koblitz (Ed.), Springer-Verlag, pages 89–103, 1996. Kleptography is a subfield of cryptovirology and is a natural extension of the theory of subliminal channels that was pioneered by Gus Simmons while at Sandia National Laboratory. G. J. Simmons, "The Prisoners' Problem and the Subliminal Channel," In Proceedings of Crypto '83, D. Chaum (Ed.), pages 51–67, Plenum Press, 1984.G. J. Simmons, "The Subliminal Channel and Digital Signatures," In Proceedings of Eurocrypt '84, T. Beth, N. Cot, I. Ingemarsson (Eds.), pages 364-378, Springer-Verlag, 1985.G. J. Simmons, "Subliminal Communication is Easy Using the DSA," In proceedings of Eurocrypt '93, T. Helleseth (Ed.), pages ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Moti Yung
Mordechai M. "Moti" Yung is a cryptographer and computer scientist known for his work on cryptovirology and kleptography. Career Yung earned his PhD from Columbia University in 1988 under the supervision of Zvi Galil. In the past, he worked at the IBM Thomas J. Watson Research Center, CertCo, RSA Laboratories, and Google. In 2016, Yung moved from Google to Snap Inc. Yung is currently a research scientist at Google. Yung is an adjunct senior research faculty member at Columbia University, and has co-advised PhD students including Gödel Prize winner Matthew K. Franklin, Jonathan Katz, and Aggelos Kiayias. Research Yung research covers primarily the area of cryptography and its applications to information security and data privacy. He has worked on defining and implementing malicious (offensive) cryptography: cryptovirology and kleptography, and on various other foundational and applied fields of cryptographic research, including: user and entity electronic authentication, in ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptotrojan
Ransomware is a type of malware from cryptovirology that threatens to publish the victim's personal data or permanently block access to it unless a ransom is paid off. While some simple ransomware may lock the system without damaging any files, more advanced malware uses a technique called cryptoviral extortion. It encrypts the victim's files, making them inaccessible, and demands a ransom payment to decrypt them. In a properly implemented cryptoviral extortion attack, recovering the files without the decryption key is an intractable problem – and difficult to trace digital currencies such as paysafecard or Bitcoin and other cryptocurrencies are used for the ransoms, making tracing and prosecuting the perpetrators difficult. Ransomware attacks are typically carried out using a Trojan disguised as a legitimate file that the user is tricked into downloading or opening when it arrives as an email attachment. However, one high-profile example, the WannaCry worm, traveled automat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NIST SP 800-90A
NIST SP 800-90A ("SP" stands for "''special publication''") is a publication by the National Institute of Standards and Technology with the title ''Recommendation for Random Number Generation Using Deterministic Random Bit Generators''. The publication contains the specification for three allegedly cryptographically secure pseudorandom number generators for use in cryptography: Hash DRBG (based on hash functions), HMAC DRBG (based on HMAC), and CTR DRBG (based on block ciphers in counter mode). Since June 24, 2015, the current version of the publication is Revision 1. Earlier versions included a fourth generator, Dual_EC_DRBG (based on elliptic curve cryptography). Dual_EC_DRBG was later reported to probably contain a kleptographic backdoor inserted by the United States National Security Agency (NSA), while the other three random number generators are accepted as uncontroversial and secure by multiple cryptographers. As a work of the US Federal Government, NIST SP 800-90A is i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Pseudo-random Number Generator
A cryptographically secure pseudorandom number generator (CSPRNG) or cryptographic pseudorandom number generator (CPRNG) is a pseudorandom number generator (PRNG) with properties that make it suitable for use in cryptography. It is also loosely known as a cryptographic random number generator (CRNG) (see Random number generation § "True" vs. pseudo-random numbers). Most cryptographic applications require random numbers, for example: * key generation * nonces * salts in certain signature schemes, including ECDSA, RSASSA-PSS The "quality" of the randomness required for these applications varies. For example, creating a nonce in some protocols needs only uniqueness. On the other hand, the generation of a master key requires a higher quality, such as more entropy. And in the case of one-time pads, the information-theoretic guarantee of perfect secrecy only holds if the key material comes from a true random source with high entropy, and thus any kind of pseudorandom number gene ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dual EC DRBG
Dual_EC_DRBG (Dual Elliptic Curve Deterministic Random Bit Generator) is an algorithm that was presented as a cryptographically secure pseudorandom number generator (CSPRNG) using methods in elliptic curve cryptography. Despite wide public criticism, including the public identification of a backdoor, it was for seven years one of four CSPRNGs standardized in NIST SP 800-90A as originally published circa June 2006, until it was withdrawn in 2014. Weakness: a potential backdoor Weaknesses in the cryptographic security of the algorithm were known and publicly criticised well before the algorithm became part of a formal standard endorsed by the ANSI, ISO, and formerly by the National Institute of Standards and Technology (NIST). One of the weaknesses publicly identified was the potential of the algorithm to harbour a kleptographic backdoor advantageous to those who know about it—the United States government's National Security Agency (NSA)—and no one else. In 2013, ''Th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
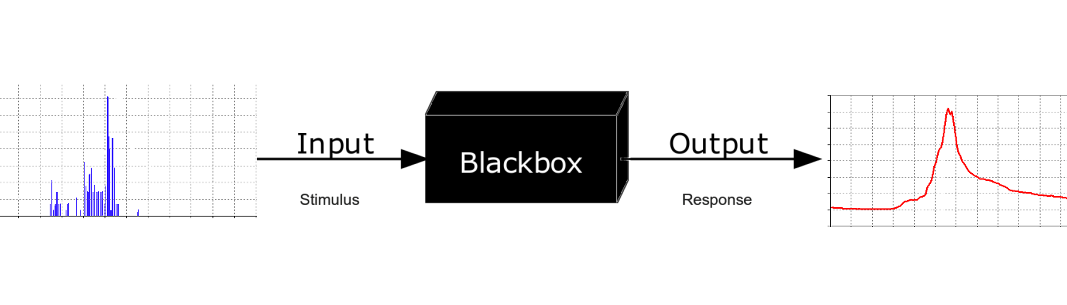
Black Box
In science, computing, and engineering, a black box is a system which can be viewed in terms of its inputs and outputs (or transfer characteristics), without any knowledge of its internal workings. Its implementation is "opaque" (black). The term can be used to refer to many inner workings, such as those of a transistor, an engine, an algorithm, the human brain, or an institution or government. To analyse an open system with a typical "black box approach", only the behavior of the stimulus/response will be accounted for, to infer the (unknown) ''box''. The usual representation of this ''black box system'' is a data flow diagram centered in the box. The opposite of a black box is a system where the inner components or logic are available for inspection, which is most commonly referred to as a white box (sometimes also known as a "clear box" or a "glass box"). History The modern meaning of the term "black box" seems to have entered the English language around 1945. In electr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kleptographic Attack
Kleptography is the study of stealing information securely and subliminally. The term was introduced by Adam Young and Moti Yung in the Proceedings of Advances in Cryptology—Crypto '96.A. Young, M. Yung, "The Dark Side of Black-Box Cryptography, or: Should we trust Capstone?" In Proceedings of Crypto '96, Neal Koblitz (Ed.), Springer-Verlag, pages 89–103, 1996. Kleptography is a subfield of cryptovirology and is a natural extension of the theory of subliminal channels that was pioneered by Gus Simmons while at Sandia National Laboratory. G. J. Simmons, "The Prisoners' Problem and the Subliminal Channel," In Proceedings of Crypto '83, D. Chaum (Ed.), pages 51–67, Plenum Press, 1984.G. J. Simmons, "The Subliminal Channel and Digital Signatures," In Proceedings of Eurocrypt '84, T. Beth, N. Cot, I. Ingemarsson (Eds.), pages 364-378, Springer-Verlag, 1985.G. J. Simmons, "Subliminal Communication is Easy Using the DSA," In proceedings of Eurocrypt '93, T. Helleseth (Ed.), pages ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IPsec
In computing, Internet Protocol Security (IPsec) is a secure network protocol suite that authenticates and encrypts packets of data to provide secure encrypted communication between two computers over an Internet Protocol network. It is used in virtual private networks (VPNs). IPsec includes protocols for establishing mutual authentication between agents at the beginning of a session and negotiation of cryptographic keys to use during the session. IPsec can protect data flows between a pair of hosts (''host-to-host''), between a pair of security gateways (''network-to-network''), or between a security gateway and a host (''network-to-host''). IPsec uses cryptographic security services to protect communications over Internet Protocol (IP) networks. It supports network-level peer authentication, data origin authentication, data integrity, data confidentiality (encryption), and replay protection (protection from replay attacks). The initial IPv4 suite was developed with few s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
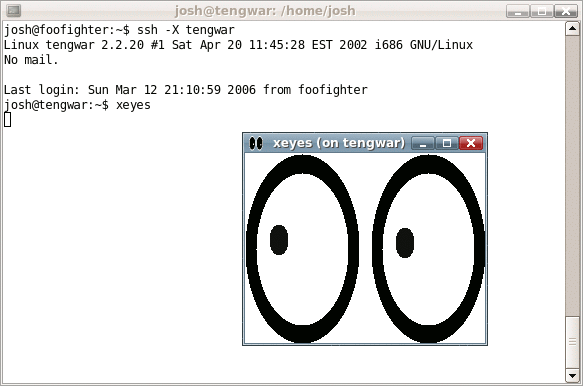
Secure Shell
The Secure Shell Protocol (SSH) is a cryptographic network protocol for operating network services securely over an unsecured network. Its most notable applications are remote login and command-line execution. SSH applications are based on a client–server architecture, connecting an SSH client instance with an SSH server. SSH operates as a layered protocol suite comprising three principal hierarchical components: the ''transport layer'' provides server authentication, confidentiality, and integrity; the ''user authentication protocol'' validates the user to the server; and the ''connection protocol'' multiplexes the encrypted tunnel into multiple logical communication channels. SSH was designed on Unix-like operating systems, as a replacement for Telnet and for unsecured remote Unix shell protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext transmission of authentication tokens. SSH was f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Sockets Layer
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible. The TLS protocol aims primarily to provide security, including privacy (confidentiality), integrity, and authenticity through the use of cryptography, such as the use of certificates, between two or more communicating computer applications. It runs in the presentation layer and is itself composed of two layers: the TLS record and the TLS handshake protocols. The closely related Datagram Transport Layer Security (DTLS) is a communications protocol providing security to datagram-based applications. In technical writing you often you will see references to (D)TLS when it applies to both versions. TLS is a proposed Internet Engineering Task Force (IETF) standard, first defined in 1999, and the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |