|
FLAIM
FLAIM (Framework for Log Anonymization and Information Management) is a modular tool designed to allow computer and network log sharing through application of complex data sanitization policies.Slagell, A., Lakkaraju, K., and Luo, K., "FLAIM: A Multi-level Anonymization Framework for Computer and Network Logs," 20th USENIX Large Installation System Administration Conference (LISA '06), Washington, D.C., Dec., 2006. FLAIM is aimed at 3 different user communities. First, FLAIM can be used by the security engineer who is investigating a broad incident spanning multiple organizations. Because of the sensitivity inherent in security relevant logs, many organizations are reluctant to share them. However, this reluctance inhibits the sharing necessary to investigate intrusions that commonly span organizational boundaries. Second, anyone designing log analysis or computer forensics tools needs data with which they can test their tools. The larger and more diverse the data set, the more ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
LAIM Working Group
The LAIM (Log Anonymization and Information Management) Working Group is a NSF and ONR funded research group at the National Center for Supercomputing Applications under the direction oAdam Slagell Work from this group focuses upon ''log anonymization'' and Internet privacy. The LAIM group, established in 2005, has released 3 different ''log anonymization'' toolsCANINE and . FLAIM
FLAIM (Framework for Log Anonymization and Information Management) is a modular tool designed to allow computer and network log sharing through application of complex data sanitization policies.Slagell, A., Lakkaraju, K., and Luo, K., "F ...
[...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Privacy Software
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a '' network of networks'' that consists of private, public, academic, business, and government networks of local to global scope, linked by a broad array of electronic, wireless, and optical networking technologies. The Internet carries a vast range of information resources and services, such as the inter-linked hypertext documents and applications of the World Wide Web (WWW), electronic mail, telephony, and file sharing. The origins of the Internet date back to the development of packet switching and research commissioned by the United States Department of Defense in the 1960s to enable time-sharing of computers. The primary precursor network, the ARPANET, initially served as a backbone for interconnection of regional academic and military networks in the 1970s to enable resource sharing. The ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anonymity
Anonymity describes situations where the acting person's identity is unknown. Some writers have argued that namelessness, though technically correct, does not capture what is more centrally at stake in contexts of anonymity. The important idea here is that a person be non-identifiable, unreachable, or untrackable. Anonymity is seen as a technique, or a way of realizing, a certain other values, such as privacy, or liberty. Over the past few years, anonymity tools used on the dark web by criminals and malicious users have drastically altered the ability of law enforcement to use conventional surveillance techniques. An important example for anonymity being not only protected, but enforced by law is the vote in free elections. In many other situations (like conversation between strangers, buying some product or service in a shop), anonymity is traditionally accepted as natural. There are also various situations in which a person might choose to withhold their identity. Acts of cha ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Pcap
In the field of computer network administration, pcap is an application programming interface (API) for capturing network traffic. While the name is an abbreviation of ''packet capture'', that is not the API's proper name. Unix-like systems implement pcap in the ''libpcap'' library; for Windows, there is a port of libpcap named ''WinPcap'' that is no longer supported or developed, and a port named ''Npcap'' for Windows 7 and later that is still supported. Monitoring software may use libpcap, WinPcap, or Npcap to capture network packets traveling over a computer network and, in newer versions, to transmit packets on a network at the link layer, and to get a list of network interfaces for possible use with libpcap, WinPcap, or Npcap. The pcap API is written in C, so other languages such as Java, .NET languages, and scripting languages generally use a wrapper; no such wrappers are provided by libpcap or WinPcap itself. C++ programs may link directly to the C API or use an o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Operating Systems
An operating system (OS) is system software that manages computer hardware, software resources, and provides common services for computer programs. Time-sharing operating systems schedule tasks for efficient use of the system and may also include accounting software for cost allocation of processor time, mass storage, printing, and other resources. For hardware functions such as input and output and memory allocation, the operating system acts as an intermediary between programs and the computer hardware, although the application code is usually executed directly by the hardware and frequently makes system calls to an OS function or is interrupted by it. Operating systems are found on many devices that contain a computer from cellular phones and video game consoles to web servers and supercomputers. The dominant general-purpose personal computer operating system is Microsoft Windows with a market share of around 74.99%. macOS by Apple Inc. is in second place (14.84%), and th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UNIX-like
A Unix-like (sometimes referred to as UN*X or *nix) operating system is one that behaves in a manner similar to a Unix system, although not necessarily conforming to or being certified to any version of the Single UNIX Specification. A Unix-like application is one that behaves like the corresponding Unix command or shell. Although there are general philosophies for Unix design, there is no technical standard defining the term, and opinions can differ about the degree to which a particular operating system or application is Unix-like. Some well-known examples of Unix-like operating systems include Linux and BSD. These systems are often used on servers, as well as on personal computers and other devices. Many popular applications, such as the Apache web server and the Bash shell, are also designed to be used on Unix-like systems. One of the key features of Unix-like systems is their ability to support multiple users and processes simultaneously. This allows users to run multipl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Science Foundation
The National Science Foundation (NSF) is an independent agency of the United States government that supports fundamental research and education in all the non-medical fields of science and engineering. Its medical counterpart is the National Institutes of Health. With an annual budget of about $8.3 billion (fiscal year 2020), the NSF funds approximately 25% of all federally supported basic research conducted by the United States' colleges and universities. In some fields, such as mathematics, computer science, economics, and the social sciences, the NSF is the major source of federal backing. The NSF's director and deputy director are appointed by the President of the United States and confirmed by the United States Senate, whereas the 24 president-appointed members of the National Science Board (NSB) do not require Senate confirmation. The director and deputy director are responsible for administration, planning, budgeting and day-to-day operations of the foundation, while t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UNIX
Unix (; trademarked as UNIX) is a family of multitasking, multiuser computer operating systems that derive from the original AT&T Unix, whose development started in 1969 at the Bell Labs research center by Ken Thompson, Dennis Ritchie, and others. Initially intended for use inside the Bell System, AT&T licensed Unix to outside parties in the late 1970s, leading to a variety of both academic and commercial Unix variants from vendors including University of California, Berkeley (Berkeley Software Distribution, BSD), Microsoft (Xenix), Sun Microsystems (SunOS/Solaris (operating system), Solaris), Hewlett-Packard, HP/Hewlett Packard Enterprise, HPE (HP-UX), and IBM (IBM AIX, AIX). In the early 1990s, AT&T sold its rights in Unix to Novell, which then sold the UNIX trademark to The Open Group, an industry consortium founded in 1996. The Open Group allows the use of the mark for certified operating systems that comply with the Single UNIX Specification (SUS). Unix systems are chara ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Office Of Naval Research
The Office of Naval Research (ONR) is an organization within the United States Department of the Navy responsible for the science and technology programs of the U.S. Navy and Marine Corps. Established by Congress in 1946, its mission is to plan, foster, and encourage scientific research to maintain future naval power and preserve national security. It carries this out through funding and collaboration with schools, universities, government laboratories, nonprofit organizations, and for-profit organizations, and overseeing the Naval Research Laboratory, the corporate research laboratory for the Navy and Marine Corps. NRL conducts a broad program of scientific research, technology and advanced development. ONR Headquarters is in the Ballston neighborhood of Arlington, Virginia. ONR Global has offices overseas in Santiago, Sao Paulo, London, Prague, Singapore, and Tokyo. Overview ONR was authorized by an Act of Congress, Public Law 588, and subsequently approved by President ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
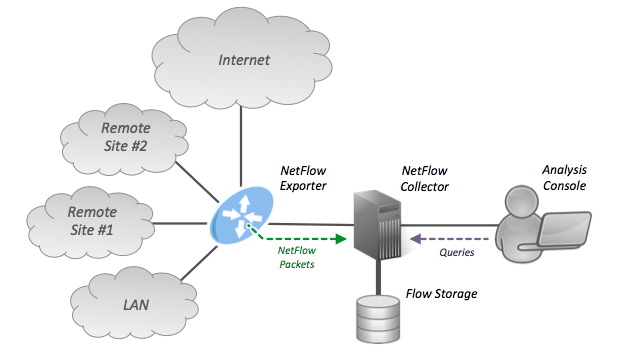
NetFlow
NetFlow is a feature that was introduced on Cisco routers around 1996 that provides the ability to collect IP network traffic as it enters or exits an interface. By analyzing the data provided by NetFlow, a network administrator can determine things such as the source and destination of traffic, class of service, and the causes of congestion. A typical flow monitoring setup (using NetFlow) consists of three main components: * Flow exporter: aggregates packets into flows and exports flow records towards one or more flow collectors. * Flow collector: responsible for reception, storage and pre-processing of flow data received from a flow exporter. * Analysis application: analyzes received flow data in the context of intrusion detection or traffic profiling, for example. Protocol description Routers and switches that support NetFlow can collect IP traffic statistics on all interfaces where NetFlow is enabled, and later export those statistics as NetFlow records toward at least on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Tcpdump
tcpdump is a data-network packet analyzer computer program that runs under a command line interface. It allows the user to display TCP/IP and other packets being transmitted or received over a network to which the computer is attached. Distributed under the BSD license, tcpdump is free software. Tcpdump works on most Unix-like operating systems: Linux, Solaris, FreeBSD, DragonFly BSD, NetBSD, OpenBSD, OpenWrt, macOS, HP-UX 11i, and AIX. In those systems, tcpdump uses the libpcap library to capture packets. The port of tcpdump for Windows is called WinDump; it uses WinPcap, the Windows version of libpcap. History tcpdump was originally written in 1988 by Van Jacobson, Sally Floyd, Vern Paxson and Steven McCanne who were, at the time, working in the Lawrence Berkeley Laboratory Network Research Group. By the late 1990s there were numerous versions of tcpdump distributed as part of various operating systems, and numerous patches that were not well coordinated. Michael Richar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |