|
Endpoint Detection And Response
Endpoint detection and response (EDR), also known as endpoint threat detection and response (ETDR), is a cybersecurity technology that continually monitors an "endpoint" (e.g. mobile phone, laptop, Internet-of-Things device) to mitigate malicious cyber threats. History In 2013, Anton Chuvakin of Gartner coined the term "endpoint threat detection and response" for "tools primarily focused on detecting and investigating suspicious activities (and traces of such) other problems on hosts/endpoints". Now, it is commonly known as "endpoint detection and response". According to the ''Endpoint Detection and Response - Global Market Outlook (2017-2026)'' report, the adoption of cloud-based and on-premises EDR solutions are going to grow 26% annually, and will be valued at $7273.26 million by 2026. According to the ''Artificial Intelligence (AI) in Cyber Security Market'' report by Zion Market Research, the role of machine learning and artificial intelligence will create a $30.9 billio ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cybersecurity
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, theft of, or damage to hardware, software, or data, as well as from the disruption or misdirection of the services they provide. The field has become of significance due to the expanded reliance on computer systems, the Internet, and wireless network standards such as Bluetooth and Wi-Fi, and due to the growth of smart devices, including smartphones, televisions, and the various devices that constitute the Internet of things (IoT). Cybersecurity is one of the most significant challenges of the contemporary world, due to both the complexity of information systems and the societies they support. Security is of especially high importance for systems that govern large-scale systems with far-reaching physical effects, such as power distributi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anton Chuvakin
Anton Chuvakin is a computer security specialist, currently a Research Director at Gartner for Technical Professionals (GTP) Security and Risk Management Strategies (SRMS) team. Formerly he was a principal at Security Warrior Consulting. Previous positions included roles of a Director of PCI Compliance Solutions at Qualys, a U.S. Vulnerability management company, a Chief Logging Evangelist with LogLogic, a U.S. Log Management and Intelligence company and a Security Strategist with netForensics, a U.S. Security information management company. A physicist by education (M.S. Moscow State University, Ph.D. State University of New York at Stony Brook), he is an author of many publications and invited talks on computer and network security and a co-author of ''"Security Warrior"'' published in 2004 by O'Reilly () and later translated and published in German, Polish and Japanese. His other books include ''"PCI Compliance"'' republished in 2009 (second edition) by Syngress Publishin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Gartner
Gartner, Inc is a technological research and consulting firm based in Stamford, Connecticut that conducts research on technology and shares this research both through private consulting as well as executive programs and conferences. Its clients include large corporations, government agencies, technology companies, and investment firms. In 2018, the company reported that its client base consisted of over 12,000 organizations in over 100 countries. As of 2022, Gartner has over 15,000 employees located in over 100 offices worldwide. It is a member of the S&P 500. History Gideon Gartner founded Gartner, Inc in 1979. Originally private, the company launched publicly as Gartner Group in 1986 before Saatchi & Saatchi acquired it in 1988. In 1990, Gartner Group was acquired by some of its executives, including Gartner himself, with funding from Bain Capital and Dun & Bradstreet. The company went public again in 1993. In 2000, the name was simplified from ''Gartner Group'' to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Comodo Cybersecurity
Xcitium, formerly known as Comodo Security Solutions, Inc., is a cybersecurity company headquartered in Bloomfield, New Jersey in the United States. History The company was founded in 1998 in the United Kingdom by Melih Abdulhayoğlu. The company relocated to the United States in 2004. Its products are focused on computer and internet security. The firm operates a certificate authority that issues SSL certificates. The company also helped on setting standards by contributing to the IETF (Internet Engineering Task Force) DNS Certification Authority Authorization (CAA) Resource Record. In October 2017, Francisco Partners acquired Comodo Certification Authority (Comodo CA) from Comodo Security Solutions, Inc. Francisco Partners rebranded Comodo CA in November 2018 to Sectigo. The change in name came less than a year after Comodo CA was acquired by Francisco Partners. On June 28, 2018, the new organization announced that it was expanding from TLS/SSL certificates into IoT secur ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OpenEDR
OpenEDR is an open-source initiative started by Xcitium. OpenEDR is a platform that analyzes at base-security-event level and generates reports for IT staff members. The source code is open source and available on GitHub GitHub, Inc. () is an Internet hosting service for software development and version control using Git. It provides the distributed version control of Git plus access control, bug tracking, software feature requests, task management, cont .... Components * Runtime components * System Monitor * File-system mini-filter * Low-level process monitoring component * Low-level registry monitoring component * Self-protection provider * Network monitor References {{Reflist Security software Free and open-source software ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Commons Clause
Source-available software is software released through a source code distribution model that includes arrangements where the source can be viewed, and in some cases modified, but without necessarily meeting the criteria to be called open-source. The licenses associated with the offerings range from allowing code to be viewed for reference to allowing code to be modified and redistributed for both commercial and non-commercial purposes. Distinction from free and open-source software Any software is source-available software as long its source code is distributed along with it, even if the user has no legal rights to use, share, modify or even compile it. It is possible for a software to be both source-available software and proprietary software (For example: Id Software Doom). In contrast, the definitions of free software and open-source software are much narrower. Free software and/or open-source software is also always ''source-available software'', but not all source-avai ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Open-source Software
Open-source software (OSS) is computer software that is released under a license in which the copyright holder grants users the rights to use, study, change, and distribute the software and its source code to anyone and for any purpose. Open-source software may be developed in a collaborative public manner. Open-source software is a prominent example of open collaboration, meaning any capable user is able to participate online in development, making the number of possible contributors indefinite. The ability to examine the code facilitates public trust in the software. Open-source software development can bring in diverse perspectives beyond those of a single company. A 2008 report by the Standish Group stated that adoption of open-source software models has resulted in savings of about $60 billion per year for consumers. Open source code can be used for studying and allows capable end users to adapt software to their personal needs in a similar way user scripts a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Advanced Persistent Threat
An advanced persistent threat (APT) is a stealthy threat actor, typically a nation state or state-sponsored group, which gains unauthorized access to a computer network and remains undetected for an extended period. In recent times, the term may also refer to non-state-sponsored groups conducting large-scale targeted intrusions for specific goals. Such threat actors' motivations are typically political or economic. Every major business sector has recorded instances of cyberattacks by advanced actors with specific goals, whether to steal, spy, or disrupt. These targeted sectors include government, defense, financial services, legal services, industrial, telecoms, consumer goods and many more. Some groups utilize traditional espionage vectors, including social engineering, human intelligence and infiltration to gain access to a physical location to enable network attacks. The purpose of these attacks is to install custom malware (malicious software). The median "dwell-time", th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
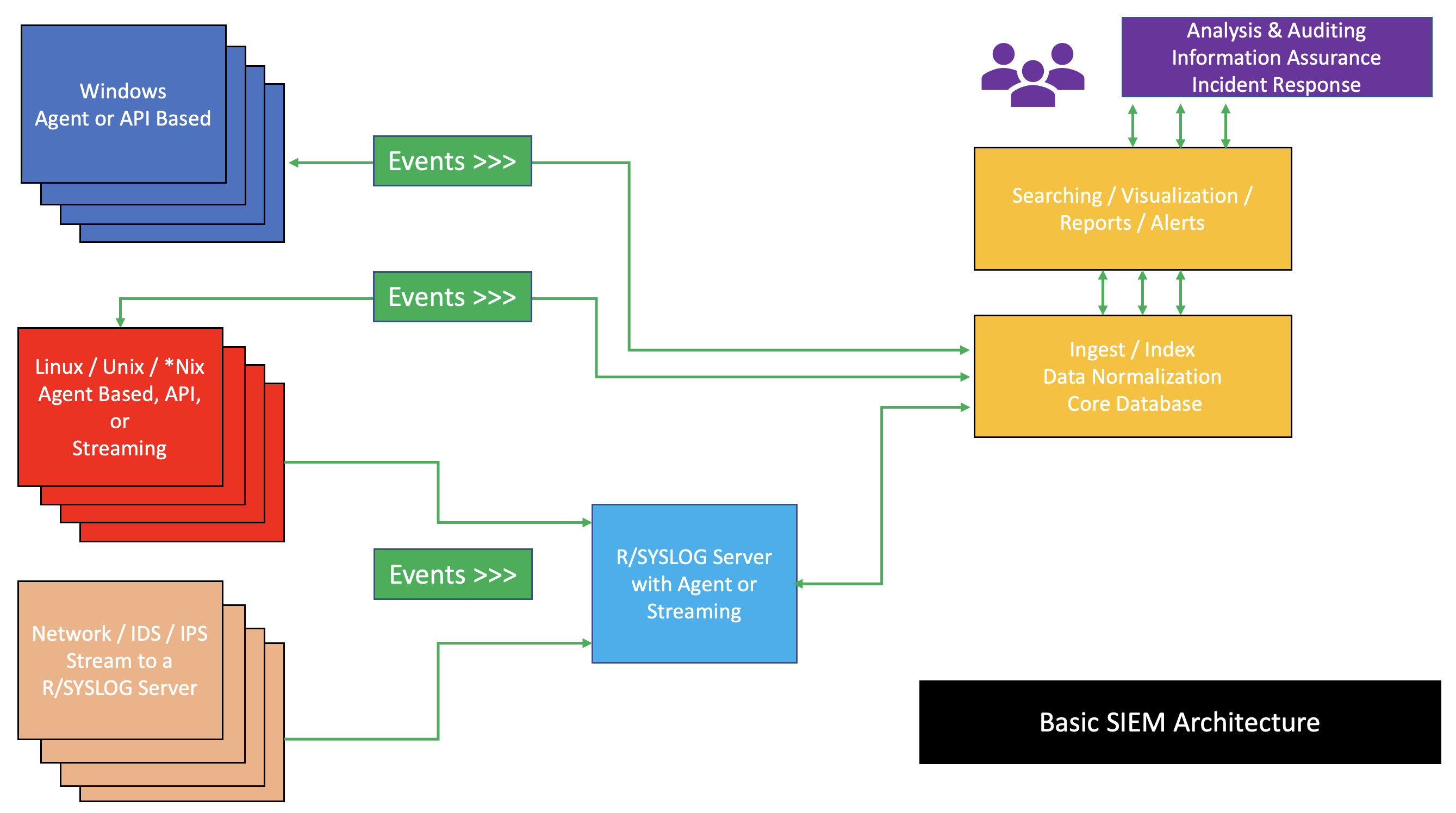
Security Information And Event Management
Security information and event management (SIEM) is a field within the field of computer security, where software products and services combine security information management (SIM) and security event management (SEM). They provide real-time analysis of security alerts generated by applications and network hardware. Vendors sell SIEM as software, as appliances, or as managed services; these products are also used to log security data and generate reports for compliance purposes. The term and the initialism SIEM was coined by Mark Nicolett and Amrit Williams of Gartner in 2005. History Monitoring system logs has grown more prevalent as complex cyber-attacks force compliance and regulatory mechanisms to mandate logging security controls within a Risk Management Framework. Logging levels of a system started with the primary function of troubleshooting system errors or debugging code compiled and run. As operating systems and networks have increased in complexity, so has the event ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Endpoint Security
Endpoint security or endpoint protection is an approach to the protection of computer networks that are remotely bridged to client devices. The connection of endpoint devices such as laptops, tablets, mobile phones, Internet-of-things devices, and other wireless devices to corporate networks creates attack paths for security threats. Endpoint security attempts to ensure that such devices follow a definite level of compliance to standards. The endpoint security space has evolved during the 2010s away from limited antivirus software and into a more advanced, comprehensive defense. This includes next-generation antivirus, threat detection, investigation, and response, device management, data leak protection (DLP), and other considerations to face evolving threats. Corporate network security Endpoint security management is a software approach that helps to identify and manage the users' computer and data access over a corporate network. This allows the network administrator to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Loss Prevention Software
Data loss prevention (DLP) software detects potential data breaches/data ex-filtration transmissions and prevents them by monitoring, detecting and blocking sensitive data while ''in use'' (endpoint actions), ''in motion'' (network traffic), and ''at rest'' (data storage). The terms " data loss" and "data leak" are related and are often used interchangeably.Asaf Shabtai, Yuval Elovici, Lior Rokach,A Survey of Data Leakage Detection and Prevention Solutions Springer-Verlag New York Incorporated, 2012 Data loss incidents turn into data leak incidents in cases where media containing sensitive information is lost and subsequently acquired by an unauthorized party. However, a data leak is possible without losing the data on the originating side. Other terms associated with data leakage prevention are information leak detection and prevention (ILDP), information leak prevention (ILP), content monitoring and filtering (CMF), information protection and control (IPC) and extrusion preventio ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |