|
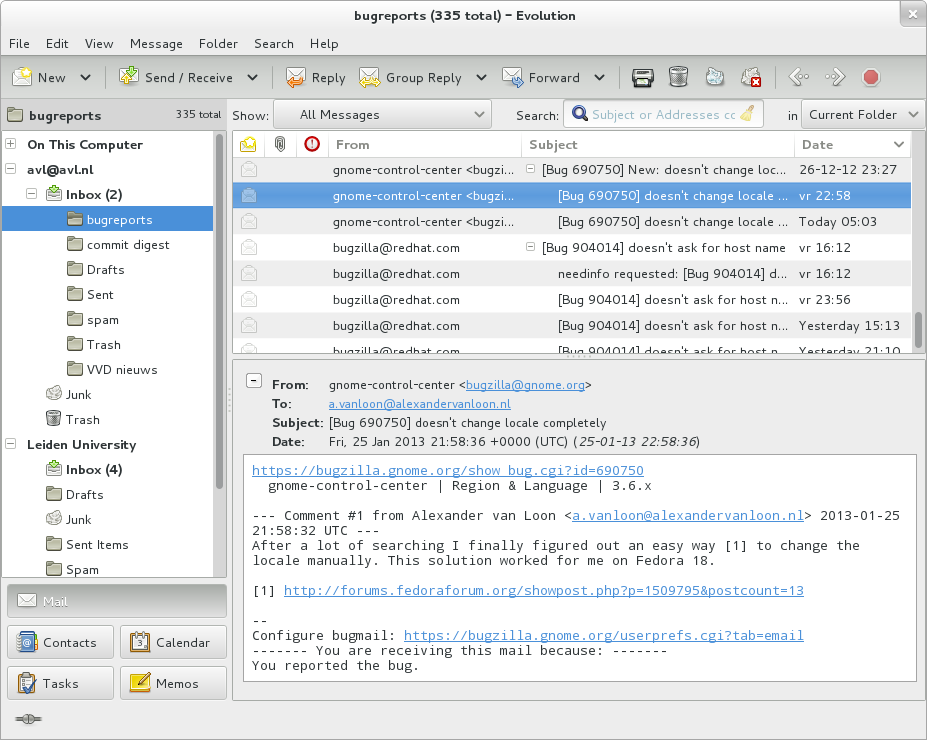
Email Box
A mailboxISO/IEC 2382:2015 (also electronic mailbox, email box, email mailbox, e-mailbox) is the destination to which electronic mail messages are delivered. It is the equivalent of a letter box in the postal system. Definitions A mailbox is identified by an email address. However, not all email addresses correspond to a storage facility. The term ''pseudo-mailbox'' is sometimes used to refer to an address that does not correspond to a definitive mail store. Email forwarding may be applied to reach end recipients from such addresses. Electronic mailing lists and email aliases are typical examples. RFC 5321, defines an ''email address'' as a character string that identifies a user to whom mail will be sent or a location into which mail will be deposited. The term ''mailbox'' refers to that depository. In that sense, the terms ''mailbox'' and ''address'' can be used interchangeably. RFC 5322 defines a mailbox as follows: ''A mailbox receives mail. It is a 'conceptual entity' that d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Electronic Mail
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronics, electronic (digital media, digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence ''wikt:e-#Etymology 2, e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet access, Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email Server (computing), servers accept, forward, deliver, and store ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Bomb
On Internet usage, an email bomb is a form of net abuse that sends large volumes of email to an address to overflow the mailbox, overwhelm the server where the email address is hosted in a denial-of-service attack (DoS attack) or as a smoke screen to distract the attention from important email messages indicating a security breach.Dima BekermanHow Registration Bots Concealed the Hacking of My Amazon Account Application Security, Industry Perspective, December 1st 2016, In: amperva.com/blog Methods There are three methods of perpetrating an email bomb: mass mailing, list linking and zip bombing. Mass mailing Mass mailing consists of sending numerous duplicate emails to the same email address. These types of mail bombs are simple to design but their extreme simplicity means they can be easily detected by spam filters. Email-bombing using mass mailing is also commonly performed as a DDoS attack by employing the use of botnets; hierarchical networks of computers compromised by ma ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
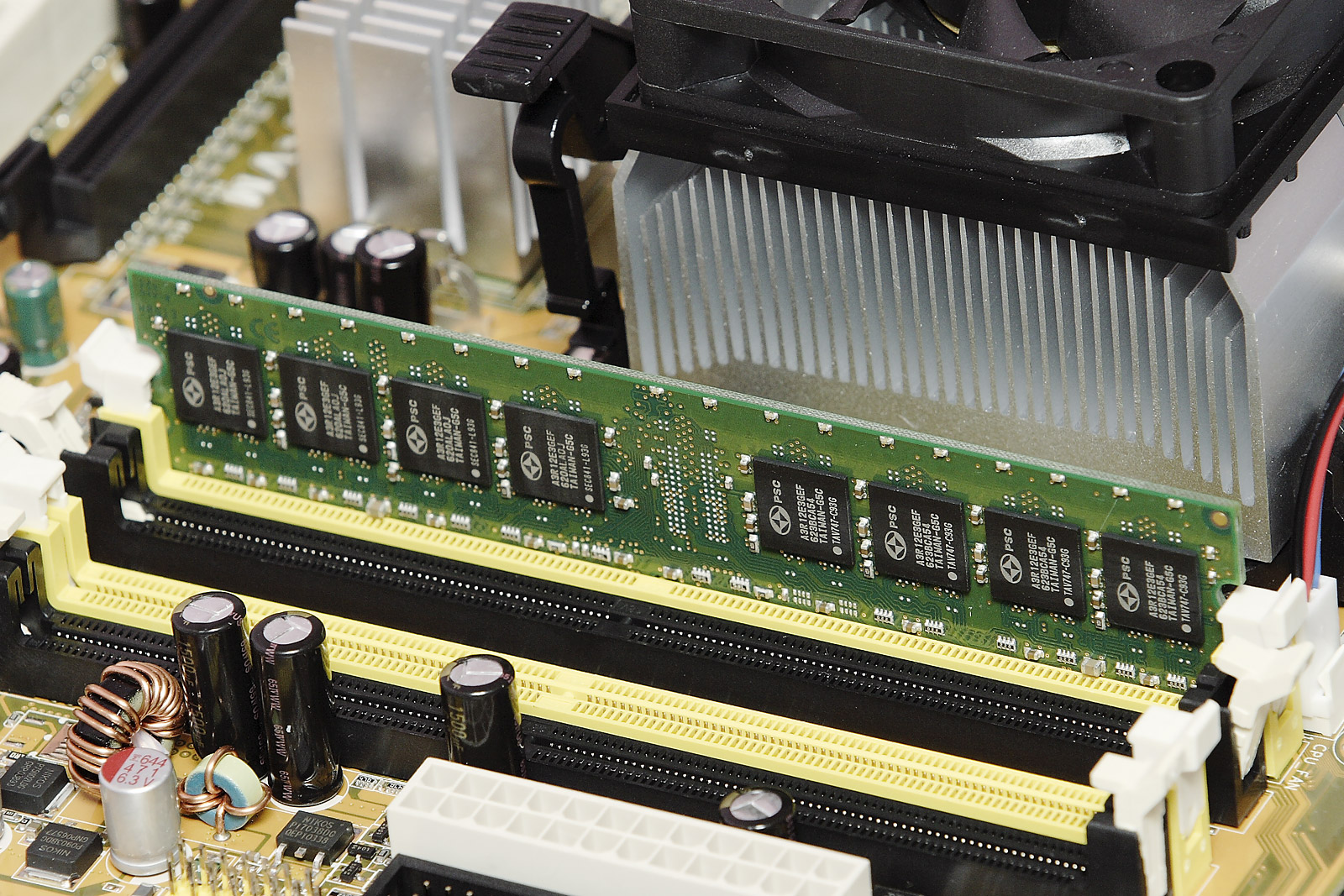
Storage System
Computer data storage is a technology consisting of computer components and recording media that are used to retain digital data. It is a core function and fundamental component of computers. The central processing unit (CPU) of a computer is what manipulates data by performing computations. In practice, almost all computers use a storage hierarchy, which puts fast but expensive and small storage options close to the CPU and slower but less expensive and larger options further away. Generally, the fast volatile technologies (which lose data when off power) are referred to as "memory", while slower persistent technologies are referred to as "storage". Even the first computer designs, Charles Babbage's Analytical Engine and Percy Ludgate's Analytical Machine, clearly distinguished between processing and memory (Babbage stored numbers as rotations of gears, while Ludgate stored numbers as displacements of rods in shuttles). This distinction was extended in the Von Neumann arch ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Filtering
Email filtering is the processing of email to organize it according to specified criteria. The term can apply to the intervention of human intelligence, but most often refers to the automatic processing of messages at an SMTP server, possibly applying anti-spam techniques. Filtering can be applied to incoming emails as well as to outgoing ones. Depending on the calling environment, email filtering software can reject an item at the initial SMTP connection stage or pass it through unchanged for delivery to the user's mailbox. It is also possible to redirect the message for delivery elsewhere, quarantine it for further checking, modify it or 'tag' it in any other way. Motivation Common uses for mail filters include organizing incoming email and removal of spam and computer viruses. Mailbox providers filter outgoing email to promptly react to spam surges that may result from compromised accounts. A less common use is to inspect outgoing email at some companies to ensure that emplo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UTF-8
UTF-8 is a variable-width encoding, variable-length character encoding used for electronic communication. Defined by the Unicode Standard, the name is derived from ''Unicode'' (or ''Universal Coded Character Set'') ''Transformation Format 8-bit''. UTF-8 is capable of encoding all 1,112,064 valid character code points in Unicode using one to four one-byte (8-bit) code units. Code points with lower numerical values, which tend to occur more frequently, are encoded using fewer bytes. It was designed for backward compatibility with ASCII: the first 128 characters of Unicode, which correspond one-to-one with ASCII, are encoded using a single byte with the same binary value as ASCII, so that valid ASCII text is valid UTF-8-encoded Unicode as well. UTF-8 was designed as a superior alternative to UTF-1, a proposed variable-length encoding with partial ASCII compatibility which lacked some features including self-synchronizing code, self-synchronization and fully ASCII-compatible handling ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SMTPUTF8
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typically use SMTP only for sending messages to a mail server for relaying, and typically submit outgoing email to the mail server on port 587 or 465 per . For retrieving messages, IMAP (which replaced the older POP3) is standard, but proprietary servers also often implement proprietary protocols, e.g., Exchange ActiveSync. SMTP's origins began in 1980, building on concepts implemented on the ARPANET since 1971. It has been updated, modified and extended multiple times. The protocol version in common use today has extensible structure with various extensions for authentication, encryption, binary data transfer, and internationalized email addresses. SMTP servers commonly use the Transmission Control Protocol on port number 25 (for plaintext) and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Username
A user is a person who utilizes a computer or Computer network, network Service (systems architecture), service. A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term. Some software products provide services to other systems and have no direct end users. End user End users are the ultimate human users (also referred to as Operator (profession), operators) of a software product. The end user stands in contrast to users who support or maintain the product such as sysops, database administrators and computer technicians. The term is used to abstract and distinguish those who only use the software from the developers of the system, who enhance the software for end users. In user-centered design, it also distinguishes the software operator from the client who ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Maildir
The Maildir e-mail format is a common way of storing email messages in which each message is stored in a separate file with a unique name, and each mail folder is a file system directory. The local file system handles file locking as messages are added, moved and deleted. A major design goal of Maildir is to eliminate the need for program code to handle file locking and unlocking. __TOC__ Specifications A Maildir directory (often named Maildir) usually has three subdirectories named tmp, new, and cur. The tmp subdirectory temporarily stores e-mail messages that are in the process of being delivered. This subdirectory may also store other kinds of temporary files. The new subdirectory stores messages that have been delivered, but have not yet been seen by any mail application. The cur subdirectory stores messages that have already been seen by mail applications. Maildir++ Sam Varshavchik, the author of the Courier Mail Server and other software, wrote an extension to the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mbox
Mbox is a generic term for a family of related file formats used for holding collections of email messages. It was first implemented in Research Unix, Fifth Edition Unix. All messages in an mbox mailbox are concatenated and stored as plain text in a single file. Each message starts with the four characters "From" followed by a space (the so-called "From_ line") and the sender's email address. RFC 4155 defines that a UTC timestamp follows after another separating space character. A format similar to mbox is the MH Message Handling System. Other systems, such as Microsoft Exchange Server and the Cyrus (imapd), Cyrus IMAP server, store mailboxes in centralized databases managed by the mail system and not directly accessible by individual users. The maildir mailbox format is often cited as an alternative to the mbox format for networked email storage systems. Mail storage protocols Unlike the Internet protocols used for the exchange of email, the format used for the storage of em ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Program
A computer program is a sequence or set of instructions in a programming language for a computer to execute. Computer programs are one component of software, which also includes documentation and other intangible components. A computer program in its human-readable form is called source code. Source code needs another computer program to execute because computers can only execute their native machine instructions. Therefore, source code may be translated to machine instructions using the language's compiler. ( Assembly language programs are translated using an assembler.) The resulting file is called an executable. Alternatively, source code may execute within the language's interpreter. If the executable is requested for execution, then the operating system loads it into memory and starts a process. The central processing unit will soon switch to this process so it can fetch, decode, and then execute each machine instruction. If the source code is requested for execution, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Engineering Task Force
The Internet Engineering Task Force (IETF) is a standards organization for the Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, an international non-profit organization. Organization The IETF is organized into a large number of working groups and birds of a feather informal discussion groups, each dealing with a specific topic. The IETF operates in a bottom-up task creation mode, largely driven by these working groups. Each working group has an appointed chairperson (or sometimes several co-chairs); a charter that describes its focus; and what it is expected to produce, and when. It is open to all who want to particip ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |