|
European Institute For Computer Antivirus Research
The European Institute for Computer Antivirus Research (EICAR) was founded in 1991 as an organization aiming to further antivirus research and improving development of antivirus software. Recently EICAR has furthered its scope to include the research of malicious software (malware) other than computer viruses and extended work on other information security topics like content security, Wireless LAN security, RFID and information security awareness. EICAR also organizes international security conferences most years, as well as a number of working groups or 'task forces'. Acronym "EICAR" was originally an abbreviation for ''"European Institute for Computer Antivirus Research"'', but the organisation no longer uses that full title, and now regards "EICAR" as a self-standing name, as it has expanded into a broader range of IT Security work than just antivirus research. EICAR test file EICAR, in collaboration with CARO (Computer AntiVirus Research Organization), developed the EICAR t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect from other computer threats. In particular, modern antivirus software can protect users from malicious browser helper objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraud tools, adware, and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, advanced persistent threat (APT), and botnet DDoS attacks. History 1949–1980 period (pre-antivirus days) Although the roots of the c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan ho ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
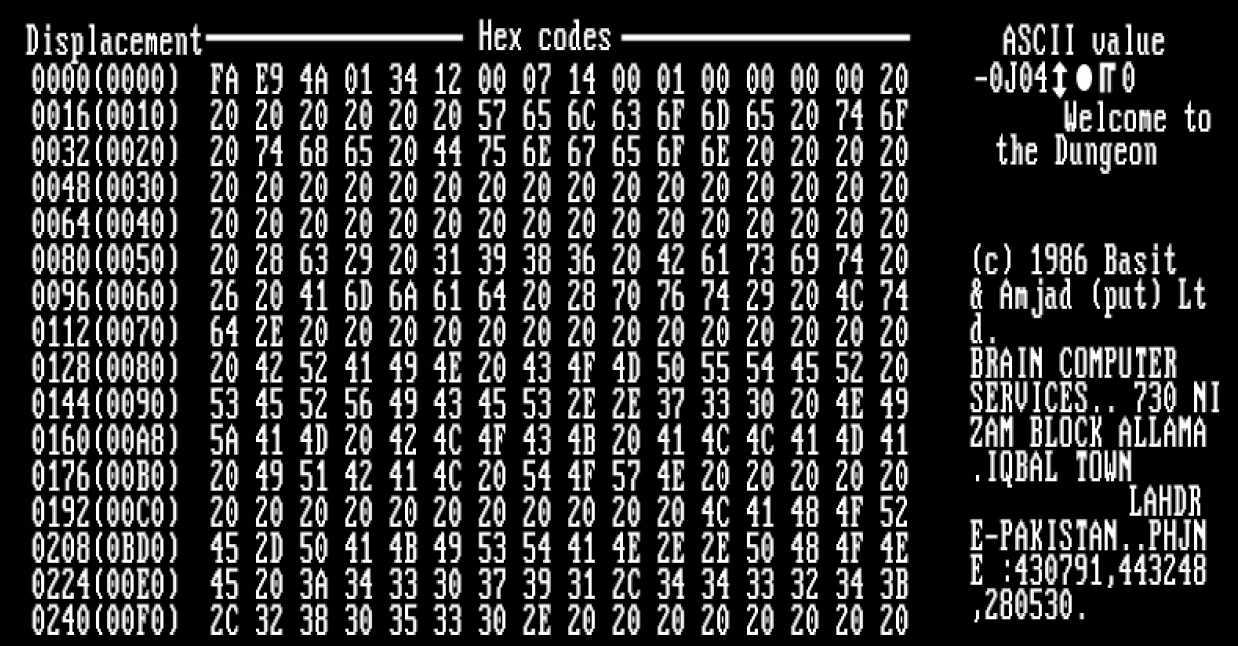
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. A computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks. Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can inclu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wireless LAN
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office building. This gives users the ability to move around within the area and remain connected to the network. Through a gateway, a WLAN can also provide a connection to the wider Internet. Wireless LANs based on the IEEE 802.11 standards are the most widely used computer networks in the world. These are commonly called Wi-Fi, which is a trademark belonging to the Wi-Fi Alliance. They are used for home and small office networks that link together laptop computers, printers, smartphones, Web TVs and gaming devices with a wireless router, which links them to the internet. Hotspots provided by routers at restaurants, coffee shops, hotels, libraries, and airports allow consumers to access the internet with portable wireless devices. History Norman ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
RFID
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder, a radio receiver and transmitter. When triggered by an electromagnetic interrogation pulse from a nearby RFID reader device, the tag transmits digital data, usually an identifying inventory number, back to the reader. This number can be used to track inventory goods. Passive tags are powered by energy from the RFID reader's interrogating radio waves. Active tags are powered by a battery and thus can be read at a greater range from the RFID reader, up to hundreds of meters. Unlike a barcode, the tag does not need to be within the line of sight of the reader, so it may be embedded in the tracked object. RFID is one method of automatic identification and data capture (AIDC). RFID tags are used in many industries. For example, an RFID tag attached to an automobile during production can be used to tra ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CARO
Caro may refer to: Places * Caro, Michigan, United States * Caro, Morbihan, France * Çaro, Pyrénées-Atlantiques, France Other uses * Caro (given name), including a list of people with the given name * Caro (surname), including a list of people with the surname * Caro (drink), a drink by Nestlé * Caro (horse) (1967–1989), a French Thoroughbred racehorse * "Caro" (Bad Bunny song), 2018 * "Caro" (L.A.X and Wizkid song), 2013 * CARO, Computer Antivirus Research Organization * Caro Ru Lushe, a fictional character in ''Magical Girl Lyrical Nanoha StrikerS'' * Caro, a Vietnamese variant of the game Gomoku * Polonez Caro or FSO Polonez, a Polish automobile See also * Frank–Caro process, used to produce cyanamide from calcium carbide and nitrogen gas in an electric furnace * Linde–Frank–Caro process, another process used to produce hydrogen from water gas * Peroxymonosulfuric acid Peroxymonosulfuric acid, , also known as persulfuric acid, peroxysulfuric acid, or Ca ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EICAR Test File
The EICAR Anti-Virus Test File or EICAR test file is a computer file that was developed by the European Institute for Computer Antivirus Research (EICAR) and Computer Antivirus Research Organization (CARO), to test the response of computer antivirus (AV) programs. Instead of using real malware, which could cause real damage, this test file allows people to test anti-virus software without having to use a real computer virus. Anti-virus programmers set the EICAR string as a verified virus, similar to other identified signatures. A compliant virus scanner, when detecting the file, will respond in more or less the same manner as if it found a harmful virus. Not all virus scanners are compliant, and may not detect the file even when they are correctly configured. Neither the way in which the file is detected nor the wording with which it is flagged are standardized, and may differ from the way in which real malware is flagged, but should prevent it from executing as long as it meets ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anti-Malware Testing Standards Organization
Anti-Malware Testing Standards Organization (AMTSO) is an international non-profit organization set up in 2008 to address a perceived need for improvement in the quality, relevance and objectivity of anti-malware testing methodologies. Stated objectives According to the AMTSO web site, the organization's charter lists the following objectives: * Providing a forum for discussions related to the testing of anti-malware and related products. * Developing and publicizing objective standards and best practices for testing of anti-malware and related products. * Promoting education and awareness of issues related to the testing of anti-malware and related products. * Providing tools and resources to aid standards-based testing methodologies. Organization Until 2012 AMTSO was administered by an elected and unpaid Board of Directors, with strategic and other input from an Advisory Board, and six committees to handle specific operations such as membership, fees, PR and so on. Subsequen ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect from other computer threats. In particular, modern antivirus software can protect users from malicious browser helper objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraud tools, adware, and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, advanced persistent threat (APT), and botnet DDoS attacks. History 1949–1980 period (pre-antivirus days) Although the roots of the c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Technology Organizations Based In Europe
Information is an abstract concept that refers to that which has the power to inform. At the most fundamental level information pertains to the interpretation of that which may be sensed. Any natural process that is not completely random, and any observable pattern in any medium can be said to convey some amount of information. Whereas digital signals and other data use discrete signs to convey information, other phenomena and artifacts such as analog signals, poems, pictures, music or other sounds, and currents convey information in a more continuous form. Information is not knowledge itself, but the meaning that may be derived from a representation through interpretation. Information is often processed iteratively: Data available at one step are processed into information to be interpreted and processed at the next step. For example, in written text each symbol or letter conveys information relevant to the word it is part of, each word conveys information releva ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |