|
Edge Device
An edge device is a device that provides an entry point into enterprise or service provider core networks. Examples include routers, routing switches, integrated access devices (IADs), multiplexers, and a variety of metropolitan area network (MAN) and wide area network (WAN) access devices. Edge devices also provide connections into carrier and service provider networks. An edge device that connects a local area network to a high speed switch or backbone (such as an ATM switch) may be called an ''edge concentrator''. Functions In general, edge devices are normally routers that provide authenticated access (most commonly PPPoA and PPPoE) to faster, more efficient backbone and core networks. The trend is to make the edge device smart and the core device(s) "dumb and fast", so edge routers often include quality of service (QoS) and multi-service functions to manage different types of traffic. Consequently, core networks are often designed with switches that use routing protocols ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Router (computing)
A router is a networking device that forwards data packets between computer networks. Routers perform the traffic directing functions between networks and on the global Internet. Data sent through a network, such as a web page or email, is in the form of data packets. A packet is typically forwarded from one router to another router through the networks that constitute an internetwork (e.g. the Internet) until it reaches its destination node. A router is connected to two or more data lines from different IP networks. When a data packet comes in on one of the lines, the router reads the network address information in the packet header to determine the ultimate destination. Then, using information in its routing table or routing policy, it directs the packet to the next network on its journey. The most familiar type of IP routers are home and small office routers that simply forward IP packets between the home computers and the Internet. More sophisticated routers, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Token Ring
Token Ring network IBM hermaphroditic connector with locking clip. Screen contacts are prominently visible, gold-plated signal contacts less so. Token Ring is a computer networking technology used to build local area networks. It was introduced by IBM in 1984, and standardized in 1989 as IEEE 802.5. It uses a special three-byte frame called a ''token'' that is passed around a logical ''ring'' of workstations or servers. This token passing is a channel access method providing fair access for all stations, and eliminating the collisions of contention-based access methods. Token Ring was a successful technology, particularly in corporate environments, but was gradually eclipsed by the later versions of Ethernet. History A wide range of different local area network technologies were developed in the early 1970s, of which one, the Cambridge Ring, had demonstrated the potential of a token passing ring topology, and many teams worldwide began working on their own implementations. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Networking Hardware
Networking hardware, also known as network equipment or computer networking devices, are electronic devices which are required for communication and interaction between devices on a computer network. Specifically, they mediate data transmission in a computer network.IEEE 802.3-2012 Clause 9.1 Units which are the last receiver or generate data are called hosts, end systems or data terminal equipment. Range Networking devices includes a broad range of equipment which can be classified as core network components which interconnect other network components, hybrid components which can be found in the core or border of a network and hardware or software components which typically sit on the connection point of different networks. The most common kind of networking hardware today is a copper-based Ethernet adapter which is a standard inclusion on most modern computer systems. Wireless networking has become increasingly popular, especially for portable and handheld devices. Other netwo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Voice Over IP
Voice over Internet Protocol (VoIP), also called IP telephony, is a method and group of technologies for the delivery of speech, voice communications and multimedia sessions over Internet Protocol (IP) networks, such as the Internet. The terms Internet telephony, broadband telephony, and broadband phone service specifically refer to the provisioning of communications services (voice, fax, Short Message Service, SMS, voice-messaging) over the Internet, rather than via the public switched telephone network (PSTN), also known as plain old telephone service (POTS). Overview The steps and principles involved in originating VoIP telephone calls are similar to traditional digital telephony and involve signaling, channel setup, digitization of the analog voice signals, and encoding. Instead of being transmitted over a circuit-switched network, the digital information is packetized and transmission occurs as IP packets over a packet-switched network. They transport media streams using spec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Virtual Private Networking
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The benefits of a VPN include increases in functionality, security, and management of the private network. It provides access to resources that are inaccessible on the public network and is typically used for remote workers. Encryption is common, although not an inherent part of a VPN connection. A VPN is created by establishing a virtual point-to-point connection through the use of dedicated circuits or with tunneling protocols over existing networks. A VPN available from the public Internet can provide some of the benefits of a wide area network (WAN). From a user perspective, the resources available within the private network can be accessed remotely. Types Virtual private networks may be classified into several categories: ;Remote acce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Frame Relay
Frame Relay is a standardized wide area network (WAN) technology that specifies the physical and data link layers of digital telecommunications channels using a packet switching methodology. Originally designed for transport across Integrated Services Digital Network (ISDN) infrastructure, it may be used today in the context of many other network interfaces. Network providers commonly implement Frame Relay for voice (VoFR) and data as an encapsulation technique used between local area networks (LANs) over a WAN. Each end-user gets a private line (or leased line) to a Frame Relay node. The Frame Relay network handles the transmission over a frequently changing path transparent to all end-user extensively used WAN protocols. It is less expensive than leased lines and that is one reason for its popularity. The extreme simplicity of configuring user equipment in a Frame Relay network offers another reason for Frame Relay's popularity. With the advent of Ethernet over fiber optics, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Integrated Services Digital Network
Integrated Services Digital Network (ISDN) is a set of communication standards for simultaneous digital transmission of voice, video, data, and other network services over the digitalised circuits of the public switched telephone network. Work on the standard began in 1980 at Bell Labs and was formally standardized in 1988 in the CCITT "Red Book". By the time the standard was released, newer networking systems with much greater speeds were available, and ISDN saw relatively little uptake in the wider market. One estimate suggests ISDN use peaked at a worldwide total of 25 million subscribers at a time when 1.3 billion analog lines were in use. ISDN has largely been replaced with digital subscriber line (DSL) systems of much higher performance. Prior to ISDN, the telephone system consisted of digital links like T1/ E1 on the long-distance lines between telephone company offices and analog signals on copper telephone wires to the customers, the " last mile". At the time, t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Backhaul (telecommunications)
In a hierarchical telecommunications network, the backhaul portion of the network comprises the intermediate links between the core network, or backbone network, and the small subnetworks at the ''edge'' of the network. The most common network type in which backhaul is implemented is a mobile network. A backhaul of a mobile network, also referred to as mobile-backhaul connects a cell site towards the core network. The two main methods of mobile backhaul implementations are fiber-based backhaul and wireless point-to-point backhaul. Other methods, such as copper-based wireline, satellite communications and point-to-multipoint wireless technologies are being phased out as capacity and latency requirements become higher in 4G and 5G networks. In both the technical and commercial definitions, ''backhaul'' generally refers to the side of the network that communicates with the global Internet, paid for at wholesale commercial access rates to or at an Internet exchange point or other co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
GPON
G.984, commonly known as GPON (gigabit-capable passive optical network), is a standard for passive optical networks (PON) published by the ITU-T. It is commonly used to implement the outermost link to the customer (last kilometre or last mile) of fibre-to-the-premises (FTTP) services. GPON puts requirements on the optical medium and the hardware used to access it, and defines the manner in which ethernet frames are converted to an optical signal, as well as the parameters of that signal. The bandwidth of the single connection between the OLT (optical line termination) and the ONTs ( optical network terminals) is 2.4Gbit/s down, 1.2Gbit/s up, or rarely symmetric 2.4Gbit/s, shared between up to 128 ONTs using a time-division multiple access (TDMA) protocol, which the standard defines. GPON specifies protocols for error correction ( Reed–Solomon) and encryption ( AES), and defines a protocol for line control ( OMCI) which includes authentication. Though implementations of GPON sh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
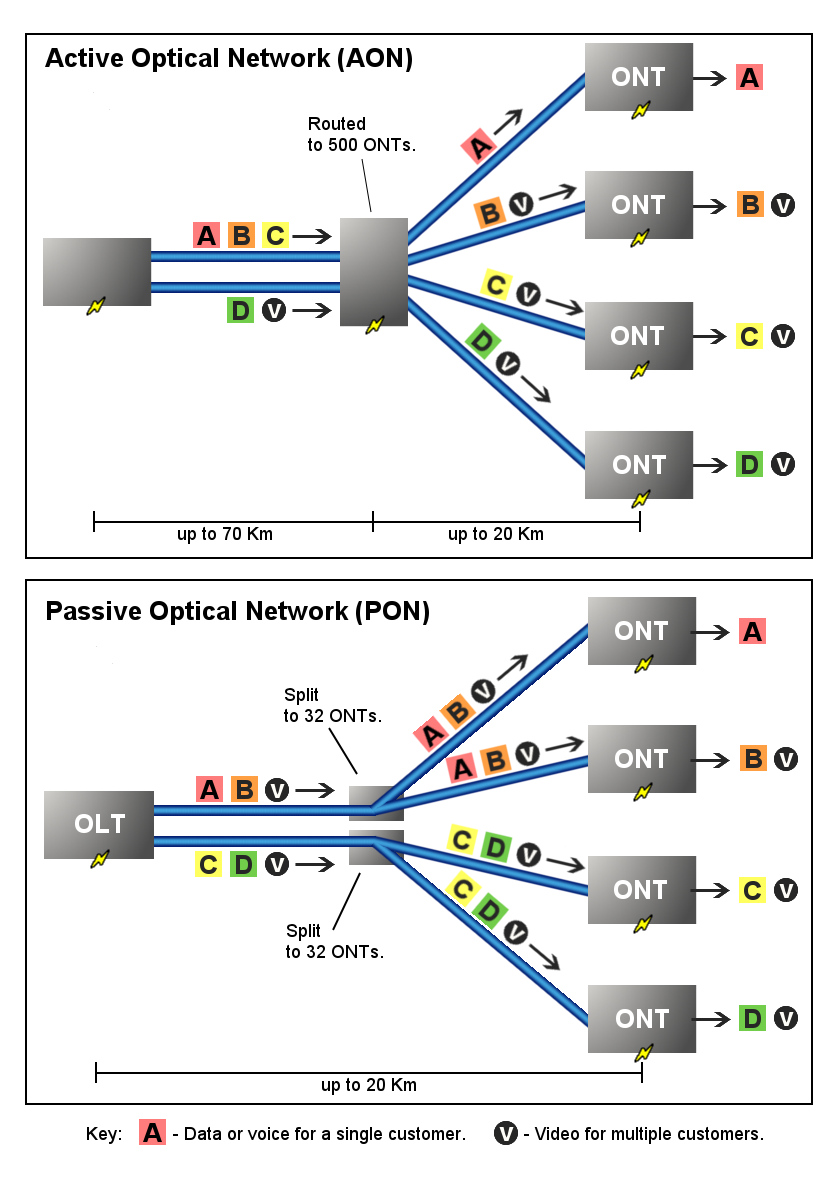
Passive Optical Network
A passive optical network (PON) is a fiber-optic telecommunications technology for delivering broadband network access to end-customers. Its architecture implements a point-to-multipoint topology in which a single optical fiber serves multiple endpoints by using unpowered (''passive'') fiber optic splitters to divide the fiber bandwidth among the endpoints. Passive optical networks are often referred to as the '' last mile'' between an Internet service provider (ISP) and its customers. Components and characteristics A passive optical network consists of an optical line terminal (OLT) at the service provider's central office (hub) and a number of optical network units (ONUs) or optical network terminals (ONTs), near end users. A PON reduces the amount of fiber and central office equipment required compared with point-to-point architectures. A passive optical network is a form of fiber-optic access network. In most cases, downstream signals are broadcast to all premises sharing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Optical Fibre
An optical fiber, or optical fibre in Commonwealth English, is a flexible, transparent fiber made by drawing glass (silica) or plastic to a diameter slightly thicker than that of a human hair. Optical fibers are used most often as a means to transmit light between the two ends of the fiber and find wide usage in fiber-optic communications, where they permit transmission over longer distances and at higher bandwidths (data transfer rates) than electrical cables. Fibers are used instead of metal wires because signals travel along them with less loss; in addition, fibers are immune to electromagnetic interference, a problem from which metal wires suffer. Fibers are also used for illumination and imaging, and are often wrapped in bundles so they may be used to carry light into, or images out of confined spaces, as in the case of a fiberscope. Specially designed fibers are also used for a variety of other applications, some of them being fiber optic sensors and fiber lasers. Op ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Asynchronous Transfer Mode
Asynchronous Transfer Mode (ATM) is a telecommunications standard defined by American National Standards Institute (ANSI) and ITU-T (formerly CCITT) for digital transmission of multiple types of traffic. ATM was developed to meet the needs of the Broadband Integrated Services Digital Network as defined in the late 1980s, and designed to integrate telecommunication networks. It can handle both traditional high-throughput data traffic and real-time, low-latency content such as telephony (voice) and video.ATM Forum, The User Network Interface (UNI), v. 3.1, , Prentice Hall PTR, 1995, page 2. ATM provides functionality that uses features of circuit switching and packet switching networks by using asynchronous time-division multiplexing.McDysan (1999), p. 287. In the OSI reference model data link layer (layer 2), the basic transfer units are called '' frames''. In ATM these frames are of a fixed length (53 octets) called ''cells''. This differs from approaches such as Internet Pro ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |