|
Domain Fronting
Domain fronting is a technique for Internet censorship circumvention that uses different domain names in different communication layers of an HTTPS connection to discreetly connect to a different target domain than is discernable to third parties monitoring the requests and connections. Due to quirks in security certificates, the redirect systems of the content delivery networks (CDNs) used as 'domain fronts', and the protection provided by HTTPS, censors are typically unable to differentiate circumvention ("domain-fronted") traffic from overt non-fronted traffic for any given domain name. As such they are forced to either allow all traffic to the domain front—including circumvention traffic—or block the domain front entirely, which may result in expensive collateral damage and has been likened to "blocking the rest of the Internet". Domain fronting does not conform to HTTP standards that require the SNI extension and HTTP Host header to contain the same domain. Many large c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Domain Fronting Letter Illustration
Domain may refer to: Mathematics *Domain of a function, the set of input values for which the (total) function is defined **Domain of definition of a partial function **Natural domain of a partial function **Domain of holomorphy of a function *Domain (mathematical analysis), an open connected set *Domain of discourse, the set of entities over which logic variables may range *Algebraic structure, Domain of an algebraic structure, the set on which the algebraic structure is defined *Domain theory, the study of certain subsets of continuous lattices that provided the first denotational semantics of the lambda calculus *Domain (ring theory), a nontrivial ring without left or right zero divisors **Integral domain, a non-trivial commutative ring without zero divisors ***Atomic domain, an integral domain in which every non-zero non-unit is a finite product of irreducible elements ***Bézout domain, an integral domain in which the sum of two principal ideals is again a principal ideal ***Eu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Diffie–Hellman Key Exchange
Diffie–Hellman key exchangeSynonyms of Diffie–Hellman key exchange include: * Diffie–Hellman–Merkle key exchange * Diffie–Hellman key agreement * Diffie–Hellman key establishment * Diffie–Hellman key negotiation * Exponential key exchange * Diffie–Hellman protocol * Diffie–Hellman handshake is a mathematical method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as conceived by Ralph Merkle and named after Whitfield Diffie and Martin Hellman. DH is one of the earliest practical examples of public key exchange implemented within the field of cryptography. Published in 1976 by Diffie and Hellman, this is the earliest publicly known work that proposed the idea of a private key and a corresponding public key. Traditionally, secure encrypted communication between two parties required that they first exchange keys by some secure physical means, such as paper key lists transported by a trusted courier. The Di ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberattack
A cyberattack is any offensive maneuver that targets computer information systems, computer networks, infrastructures, or personal computer devices. An attacker is a person or process that attempts to access data, functions, or other restricted areas of the system without authorization, potentially with malicious intent. Depending on the context, cyberattacks can be part of cyber warfare or cyberterrorism. A cyberattack can be employed by sovereign states, individuals, groups, societies or organisations and it may originate from an anonymous source. A product that facilitates a cyberattack is sometimes called a cyber weapon. Cyber attacks have increased with an alarming rate for the last few years A cyberattack may steal, alter, or destroy a specified target by hacking into a susceptible system. Cyberattacks can range from installing spyware on a personal computer to attempting to destroy the infrastructure of entire nations. Legal experts are seeking to limit the use of the ter ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Great Firewall
The Great Firewall (''GFW''; ) is the combination of legislative actions and technologies enforced by the People's Republic of China to regulate the Internet domestically. Its role in internet censorship in China is to block access to selected foreign websites and to slow down cross-border internet traffic. The Great Firewall operates by checking transmission control protocol (TCP) packets for keywords or sensitive words. If the keywords or sensitive words appear in the TCP packets, access will be closed. If one link is closed, more links from the same machine will be blocked by the Great Firewall. The effect includes: limiting access to foreign information sources, blocking foreign internet tools (e.g. Google Search, Facebook, Twitter, Wikipedia, and others) and mobile apps, and requiring foreign companies to adapt to domestic regulations. Besides censorship, the Great Firewall has also influenced the development of China's internal internet economy by giving preference to domesti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
GreatFire
GreatFire (GreatFire.org) is a website that monitors the status of websites censored by the Great Firewall of China and helps Chinese Internet users circumvent the Internet censorship in China, censorship and blockage of websites in China. Through an investigation by the Associated Press, the website was found receiving funds from the Federal government of the United States, United States government through its Open Technology Fund under Radio Free Asia. GreatFire hosts a testing system that allows visitors to test in real time the accessibility of a website from various locations within China. The organization's stated mission was to "bring transparency to the Great Firewall of China."GreatFire also provides another test systeBlocky GreatFire has worked with BBC to make the Chinese-language BBC website available to users in China, despite it being blocked by the Great Firewall, by using a method known as collateral freedom that mirrored content on widely used content delivery net ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Tor (network)
Tor, short for The Onion Router, is free and open-source software for enabling anonymous communication. It directs Internet traffic through a free, worldwide, volunteer overlay network, consisting of more than seven thousand relays, to conceal a user's location and usage from anyone performing network surveillance or traffic analysis. Using Tor makes it more difficult to trace a user's Internet activity. Tor's intended use is to protect the personal privacy of its users, as well as their freedom and ability to communicate confidentially through IP address anonymity using Tor exit nodes. History The core principle of Tor, onion routing, was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag, to protect American intelligence communications online. Onion routing is implemented by means of encryption in the application layer of the communication protocol stack ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Telex (anti-censorship System)
Telex is a research anti-censorship system that would allow users to circumvent a censor without alerting the censor to the act of circumvention. It is not ready for real users, but a proof-of-concept mock system exists. As of 2018, Telex has evolved into refraction networking. Purpose Telex complements services like Tor (anonymity network) by placing ''Telex stations'' in the network infrastructure of free countries. A client can create a TLS tunnel that is indistinguishable from allowed traffic. That way, firewalls in censored countries are neither able to detect nor to block access to specific parts of the Internet, assuming they allow access at all. See also * Domain fronting Domain fronting is a technique for Internet censorship circumvention that uses different domain names in different communication layers of an HTTPS connection to discreetly connect to a different target domain than is discernable to third parties ... References External linksOfficial website ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Amazon Web Services
Amazon Web Services, Inc. (AWS) is a subsidiary of Amazon.com, Amazon that provides Software as a service, on-demand cloud computing computing platform, platforms and Application programming interface, APIs to individuals, companies, and governments, on a metered pay-as-you-go basis. These cloud computing web services provide distributed computing processing capacity and software tools via AWS server farms. One of these services is Amazon Elastic Compute Cloud (EC2), which allows users to have at their disposal a Virtualization, virtual Computer cluster, cluster of computers, available all the time, through the Internet. AWS's virtual computers emulate most of the attributes of a real computer, including hardware central processing units (CPUs) and graphics processing units (GPUs) for processing; local/Random-access memory, RAM memory; hard-disk/Solid-state drive, SSD storage; a choice of operating systems; networking; and pre-loaded application software such as web servers, dat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
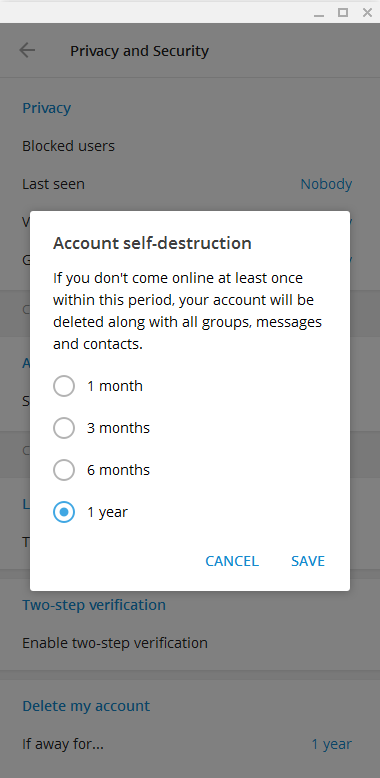
Telegram (software)
Telegram Messenger is a globally accessible freemium, cross-platform, encrypted, cloud-based and centralized instant messaging (IM) service. The application also provides optional end-to-end encrypted chats, popularly known as secret chat and video calling, VoIP, file sharing and several other features. It was launched for iOS on 14 August 2013 and Android on 20 October 2013. The servers of Telegram are distributed worldwide with five data centers in different parts of the world, while the operational center is based in Dubai, United Arab Emirates. Various client apps are available for desktop and mobile platforms including official apps for Android, iOS, Windows, macOS, and Linux (although registration requires an iOS or Android device and a working phone number). There are also two official Telegram web twin apps, WebK and WebZ, and numerous unofficial clients that make use of Telegram's protocol. Telegram's official components are open source, with the exception of the s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Tor (anonymity Network)
Tor, short for The Onion Router, is free and open-source software for enabling anonymous communication. It directs Internet traffic through a free, worldwide, volunteer overlay network, consisting of more than seven thousand relays, to conceal a user's location and usage from anyone performing network surveillance or traffic analysis. Using Tor makes it more difficult to trace a user's Internet activity. Tor's intended use is to protect the personal privacy of its users, as well as their freedom and ability to communicate confidentially through IP address anonymity using Tor exit nodes. History The core principle of Tor, onion routing, was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag, to protect American intelligence communications online. Onion routing is implemented by means of encryption in the application layer of the communication protocol stack ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Signal (software)
Signal is a cross-platform centralized encrypted instant messaging service developed by the non-profit Signal Foundation and its subsidiary, the Signal Messenger LLC. Users can send one-to-one and group messages, which can include files, voice notes, images and videos. It can also be used to make one-to-one and group voice and video calls. The Android version also optionally functions as an SMS app, but this functionality will be removed in 2023. Signal uses standard cellular telephone numbers as identifiers and secures all communications to other Signal users with end-to-end encryption. The client software includes mechanisms by which users can independently verify the identity of their contacts and the integrity of the data channel. Signal's software is free and open-source. Its mobile clients are published under the GPL-3.0-only license, while the desktop client and server are published under the AGPL-3.0-only license. The official Android app generally uses the propr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |