|
Dolev–Yao Model
The Dolev–Yao model, named after its authors Danny Dolev and Andrew Yao, is a formal model used to prove properties of interactive cryptographic protocols. The network The network is represented by a set of abstract machines that can exchange messages. These messages consist of formal terms. These terms reveal some of the internal structure of the messages, but some parts will hopefully remain opaque to the adversary. The adversary The adversary in this model can overhear, intercept, and synthesize any message and is only limited by the constraints of the cryptographic methods used. In other words: "the attacker carries the message." This omnipotence has been very difficult to model, and many threat models simplify it, as has been done for the attacker in ubiquitous computing. The algebraic model Cryptographic primitives are modeled by abstract operators. For example, asymmetric encryption for a user x is represented by the encryption function E_x and the decryption fun ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Danny Dolev
Daniel (Danny) Dolev is an Israeli computer scientist known for his research in cryptography and distributed computing. He holds the Berthold Badler Chair in Computer Science at the Hebrew University of Jerusalem and is a member of the scientific council of the European Research Council.. Biography Dolev did his undergraduate studies at the Hebrew University, earning a bachelor's degree in 1971. He then moved to the Weizmann Institute of Science, earning a master's degree in 1973 and a doctorate in 1979 under the supervision of Eli Shamir. After postdoctoral research at Stanford University and IBM Research, he joined the Hebrew University faculty in 1982. He took a second position at the IBM Almaden Research Center from 1987 to 1993, but retained his appointment at the Hebrew University. From 1998 to 2002, he was chair of the Institute of Computer Science and then Director of the School of Engineering and Computer Science at the Hebrew University. In 2011, he became the first Isra ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Andrew Yao
Andrew Chi-Chih Yao (; born December 24, 1946) is a Chinese computer scientist and computational theorist. He is currently a professor and the dean of Institute for Interdisciplinary Information Sciences (IIIS) at Tsinghua University. Yao used the minimax theorem to prove what is now known as Yao's Principle. Yao was a naturalized U.S. citizen, and worked for many years in the U.S. In 2015, together with Yang Chen-Ning, he renounced his U.S. citizenship and became an academician of the Chinese Academy of Sciences. Early life Yao was born in Shanghai, China. He completed his undergraduate education in physics at the National Taiwan University, before completing a Doctor of Philosophy in physics at Harvard University in 1972, and then a second PhD in computer science from the University of Illinois at Urbana–Champaign in 1975. Academic career Yao was an assistant professor at Massachusetts Institute of Technology (1975–1976), assistant professor at Stanford Universit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mathematical Model
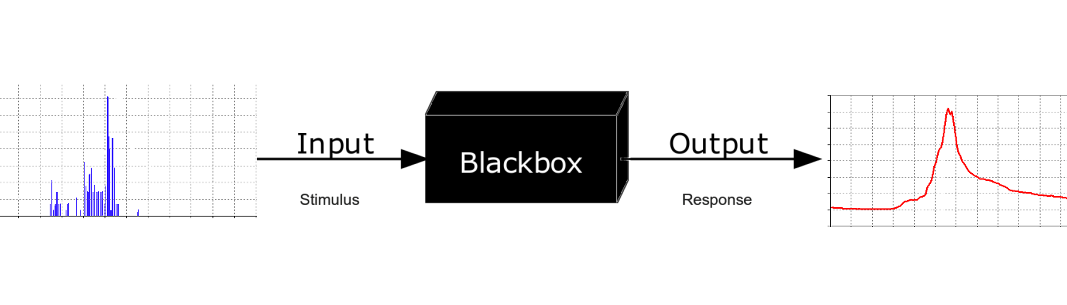
A mathematical model is a description of a system using mathematical concepts and language. The process of developing a mathematical model is termed mathematical modeling. Mathematical models are used in the natural sciences (such as physics, biology, earth science, chemistry) and engineering disciplines (such as computer science, electrical engineering), as well as in non-physical systems such as the social sciences (such as economics, psychology, sociology, political science). The use of mathematical models to solve problems in business or military operations is a large part of the field of operations research. Mathematical models are also used in music, linguistics, and philosophy (for example, intensively in analytic philosophy). A model may help to explain a system and to study the effects of different components, and to make predictions about behavior. Elements of a mathematical model Mathematical models can take many forms, including dynamical systems, statis ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Omnipotence
Omnipotence is the quality of having unlimited power. Monotheistic religions generally attribute omnipotence only to the deity of their faith. In the monotheistic religious philosophy of Abrahamic religions, omnipotence is often listed as one of a deity's characteristics, along with omniscience, omnipresence, and omnibenevolence. The presence of all these properties in a single entity has given rise to considerable theological debate, prominently including the problem of evil, the question of why such a deity would permit the existence of evil. It is accepted in philosophy and science that omnipotence can never be effectively understood. Etymology The word ''omnipotence'' derives from the Latin prefix ''omni''-, meaning "all", and the word ''potens'', meaning "potent" or "powerful". Thus the term means "all-powerful". Meanings Scholasticism The term omnipotent has been used to connote a number of different positions. These positions include, but are not limited to, th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ubiquitous Computing
Ubiquitous computing (or "ubicomp") is a concept in software engineering, hardware engineering and computer science where computing is made to appear anytime and everywhere. In contrast to desktop computing, ubiquitous computing can occur using any device, in any location, and in any format. A user interacts with the computer, which can exist in many different forms, including laptop computers, tablets, smart phones and terminals in everyday objects such as a refrigerator or a pair of glasses. The underlying technologies to support ubiquitous computing include Internet, advanced middleware, operating system, mobile code, sensors, microprocessors, new I/O and user interfaces, computer networks, mobile protocols, location and positioning, and new materials. This paradigm is also described as pervasive computing, ambient intelligence, or "everyware". Each term emphasizes slightly different aspects. When primarily concerning the objects involved, it is also known as physic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Primitive
Cryptographic primitives are well-established, low-level cryptographic algorithms that are frequently used to build cryptographic protocols for computer security systems. These routines include, but are not limited to, one-way hash functions and encryption functions. Rationale When creating cryptographic systems, designers use cryptographic primitives as their most basic building blocks. Because of this, cryptographic primitives are designed to do one very specific task in a precisely defined and highly reliable fashion. Since cryptographic primitives are used as building blocks, they must be very reliable, i.e. perform according to their specification. For example, if an encryption routine claims to be only breakable with number of computer operations, and it is broken with significantly fewer than operations, then that cryptographic primitive has failed. If a cryptographic primitive is found to fail, almost every protocol that uses it becomes vulnerable. Since creating ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Identity Function
Graph of the identity function on the real numbers In mathematics, an identity function, also called an identity relation, identity map or identity transformation, is a function that always returns the value that was used as its argument, unchanged. That is, when is the identity function, the equality is true for all values of to which can be applied. Definition Formally, if is a set, the identity function on is defined to be a function with as its domain and codomain, satisfying In other words, the function value in the codomain is always the same as the input element in the domain . The identity function on is clearly an injective function as well as a surjective function, so it is bijective. The identity function on is often denoted by . In set theory, where a function is defined as a particular kind of binary relation, the identity function is given by the identity relation, or ''diagonal'' of . Algebraic properties If is any function, then we h ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Algebra
Algebra () is one of the areas of mathematics, broad areas of mathematics. Roughly speaking, algebra is the study of mathematical symbols and the rules for manipulating these symbols in formulas; it is a unifying thread of almost all of mathematics. Elementary algebra deals with the manipulation of variable (mathematics), variables (commonly represented by Roman letters) as if they were numbers and is therefore essential in all applications of mathematics. Abstract algebra is the name given, mostly in mathematical education, education, to the study of algebraic structures such as group (mathematics), groups, ring (mathematics), rings, and field (mathematics), fields (the term is no more in common use outside educational context). Linear algebra, which deals with linear equations and linear mappings, is used for modern presentations of geometry, and has many practical applications (in weather forecasting, for example). There are many areas of mathematics that belong to algebra, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security
" \n\n\nsecurity.txt is a proposed standard for websites' security information that is meant to allow security researchers to easily report security vulnerabilities. The standard prescribes a text file called \"security.txt\" in the well known location, similar in syntax to robots.txt but intended to be machine- and human-readable, for those wishing to contact a website's owner about security issues. security.txt files have been adopted by Google, GitHub, LinkedIn, and Facebook.\n History \n\nThe Internet Draft was first submitted by Edwin Foudil in September 2017. At that time it covered four directives, \"Contact\", \"Encryption\", \"Disclosure\" and \"Acknowledgement\". Foudil expected to add further directives based on feedback. In addition, web security expert Scott Helme said he had seen positive feedback from the security community while use among the top 1 million websites was \"as low as expected right now\".\n\nIn 2019, the Cybersecurity and Infrastructure Security Agenc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Protocol
A security protocol (cryptographic protocol or encryption protocol) is an abstract or concrete protocol that performs a security-related function and applies cryptographic methods, often as sequences of cryptographic primitives. A protocol describes how the algorithms should be used and includes details about data structures and representations, at which point it can be used to implement multiple, interoperable versions of a program. Cryptographic protocols are widely used for secure application-level data transport. A cryptographic protocol usually incorporates at least some of these aspects: * Key agreement or establishment * Entity authentication * Symmetric encryption and message authentication material construction * Secured application-level data transport * Non-repudiation methods * Secret sharing methods * Secure multi-party computation For example, Transport Layer Security (TLS) is a cryptographic protocol that is used to secure web (HTTPS) connections. It has a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |