|
Digital Self-defense
Digital self-defense is the use of self-defense strategies by Internet users to ensure digital security; that is to say, the protection of confidential personal electronic information. Internet security software provides initial protection by setting up a firewall, as well as scanning computers for malware, viruses, Trojan horses, worms and spyware. However information at most risk includes personal details such as birthdates, phone numbers, bank account, schooling details, sexuality, religious affiliations, email addresses and passwords. This information is often openly revealed in social networking sites, leaving Internet users vulnerable to social engineering and possibly Internet crime. Mobile devices, especially those with Wi-Fi, allow this information to be shared inadvertently. Digital self-defense requires Internet users to take an active part in guarding their own personal information. Four key strategies are frequently suggested to assist that protection. Comp ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Self-defense
Self-defense (self-defence primarily in Commonwealth English) is a countermeasure that involves defending the health and well-being of oneself from harm. The use of the right of self-defense as a legal justification for the use of force in times of danger is available in many jurisdictions. Physical Physical self-defense is the use of physical force to counter an immediate threat of violence. Such force can be either armed or unarmed. In either case, the chances of success depend on various parameters, related to the severity of the threat on one hand, but also on the mental and physical preparedness of the defender. Unarmed Many styles of martial arts are practiced for self-defense or include self-defense techniques. Some styles train primarily for self-defense, while other combat sports can be effectively applied for self-defense. Some martial arts train how to escape from a knife or gun situation or how to break away from a punch, while others train how to attack. To ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
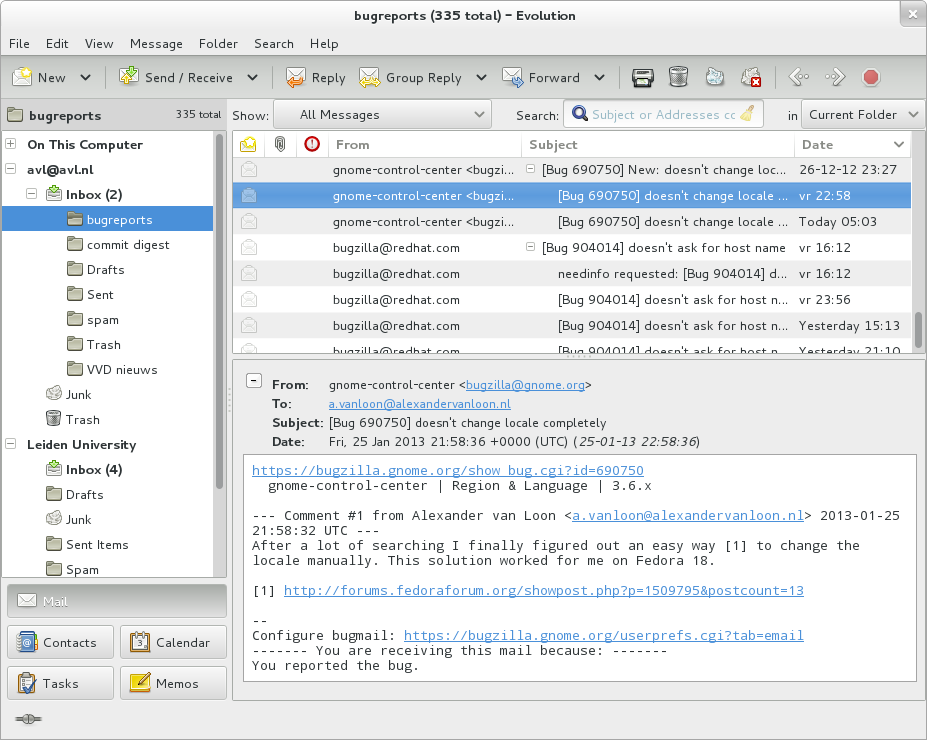
Email Address
An email address identifies an email box to which messages are delivered. While early messaging systems used a variety of formats for addressing, today, email addresses follow a set of specific rules originally standardized by the Internet Engineering Task Force (IETF) in the 1980s, and updated by . The term email address in this article refers to just the ''addr-spec'' in Section 3.4 of RFC 5322. The RFC defines ''address'' more broadly as either a ''mailbox'' or ''group''. A ''mailbox'' value can be either a ''name-addr'', which contains a ''display-name'' and ''addr-spec'', or the more common ''addr-spec'' alone. An email address, such as ''john.smith@example.com'', is made up from a local-part, the symbol @, and a ''domain'', which may be a domain name or an IP address enclosed in brackets. Although the standard requires the local part to be case-sensitive, it also urges that receiving hosts deliver messages in a case-independent manner, e.g., that the mail system in the domain ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microsoft
Microsoft Corporation is an American multinational technology corporation producing computer software, consumer electronics, personal computers, and related services headquartered at the Microsoft Redmond campus located in Redmond, Washington, United States. Its best-known software products are the Windows line of operating systems, the Microsoft Office suite, and the Internet Explorer and Edge web browsers. Its flagship hardware products are the Xbox video game consoles and the Microsoft Surface lineup of touchscreen personal computers. Microsoft ranked No. 21 in the 2020 Fortune 500 rankings of the largest United States corporations by total revenue; it was the world's largest software maker by revenue as of 2019. It is one of the Big Five American information technology companies, alongside Alphabet, Amazon, Apple, and Meta. Microsoft was founded by Bill Gates and Paul Allen on April 4, 1975, to develop and sell BASIC interpreters for the Altair 8800. It rose to do ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Password Strength
Password strength is a measure of the effectiveness of a password against guessing or brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to the password would need, on average, to guess it correctly. The strength of a password is a function of length, complexity, and unpredictability. Using strong passwords lowers overall risk of a security breach, but strong passwords do not replace the need for other effective security controls. The effectiveness of a password of a given strength is strongly determined by the design and implementation of the factors (knowledge, ownership, inherence). The first factor is the main focus in this article. The rate at which an attacker can submit guessed passwords to the system is a key factor in determining system security. Some systems impose a time-out of several seconds after a small number (e.g. three) of failed password entry attempts. In the absence of other vulnerabilities, such s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Username
A user is a person who utilizes a computer or Computer network, network Service (systems architecture), service. A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term. Some software products provide services to other systems and have no direct end users. End user End users are the ultimate human users (also referred to as Operator (profession), operators) of a software product. The end user stands in contrast to users who support or maintain the product such as sysops, database administrators and computer technicians. The term is used to abstract and distinguish those who only use the software from the developers of the system, who enhance the software for end users. In user-centered design, it also distinguishes the software operator from the client who ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Throw-away Account
Disposable email addressing, also known as DEA or dark mail, refers to an approach which involves a unique email address being used for every contact, entity, or for a limited number of times or uses. The benefit is that if anyone compromises the address or utilizes it in connection with email abuse, the address owner can easily cancel (or "dispose" of) it without affecting any of their other contacts. Uses Disposable email addressing sets up a different, unique email address for every sender/recipient combination. It operates most usefully in scenarios where someone may sell or release an email address to spam lists or to other unscrupulous entities. The most common situations of this type involve online registration for sites offering discussion groups, bulletin boards, chat rooms, online shopping, and file hosting services. At a time when email spam has become an everyday nuisance, and when identity theft threatens, DEAs can serve as a convenient tool for protecting Internet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hotmail
Outlook.com is a webmail service that is part of the Microsoft 365 product family. It offers mail, Calendaring software, calendaring, Address book, contacts, and Task management, tasks services. Founded in 1996 by Sabeer Bhatia and Jack Smith (Hotmail), Jack Smith as Hotmail, it was acquired by Microsoft in 1997 for an estimated $400 million and relaunched as ''MSN Hotmail'', later rebranded to ''Windows Live Hotmail'' as part of the Windows Live suite of products. Microsoft phased out Hotmail in October 2011, relaunching the service as Outlook.com in 2012. History Launch of Hotmail Hotmail service was founded by Sabeer Bhatia and Jack Smith (Hotmail), Jack Smith, and was one of the first webmail services on the Internet along with RocketMail, Four11's RocketMail (later Yahoo! Mail). It was commercially launched on July 4, 1996, symbolizing "freedom" from Internet service provider, ISP-based email and the ability to access a user's inbox from anywhere in the world. The name ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Google
Google LLC () is an American multinational technology company focusing on search engine technology, online advertising, cloud computing, computer software, quantum computing, e-commerce, artificial intelligence, and consumer electronics. It has been referred to as "the most powerful company in the world" and one of the world's most valuable brands due to its market dominance, data collection, and technological advantages in the area of artificial intelligence. Its parent company Alphabet is considered one of the Big Five American information technology companies, alongside Amazon, Apple, Meta, and Microsoft. Google was founded on September 4, 1998, by Larry Page and Sergey Brin while they were PhD students at Stanford University in California. Together they own about 14% of its publicly listed shares and control 56% of its stockholder voting power through super-voting stock. The company went public via an initial public offering (IPO) in 2004. In 2015, Google was reor ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Yahoo
Yahoo! (, styled yahoo''!'' in its logo) is an American web services provider. It is headquartered in Sunnyvale, California and operated by the namesake company Yahoo! Inc. (2017–present), Yahoo Inc., which is 90% owned by investment funds managed by Apollo Global Management and 10% by Verizon Communications. It provides a web portal, search engine Yahoo! Search, Yahoo Search, and related services, including My Yahoo!, Yahoo! Mail, Yahoo Mail, Yahoo! News, Yahoo News, Yahoo! Finance, Yahoo Finance, Yahoo! Sports, Yahoo Sports and its advertising platform, Yahoo! Native. Yahoo was established by Jerry Yang and David Filo in January 1994 and was one of the pioneers of the early Internet era in the 1990s. However, usage declined in the late 2000s as some services discontinued and it lost market share to Facebook and Google. History Founding In January 1994, Yang and Filo were electrical engineering graduate students at Stanford University, when they created a website named ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wi-Fi
Wi-Fi () is a family of wireless network protocols, based on the IEEE 802.11 family of standards, which are commonly used for local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio waves. These are the most widely used computer networks in the world, used globally in home and small office networks to link desktop and laptop computers, tablet computers, smartphones, smart TVs, printers, and smart speakers together and to a wireless router to connect them to the Internet, and in wireless access points in public places like coffee shops, hotels, libraries and airports to provide visitors with Internet access for their mobile devices. ''Wi-Fi'' is a trademark of the non-profit Wi-Fi Alliance, which restricts the use of the term ''Wi-Fi Certified'' to products that successfully complete interoperability certification testing. the Wi-Fi Alliance consisted of more than 800 companies from around the world. over 3.05 billion ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Crime
A cybercrime is a crime that involves a computer or a computer network.Moore, R. (2005) "Cyber crime: Investigating High-Technology Computer Crime," Cleveland, Mississippi: Anderson Publishing. The computer may have been used in committing the crime, or it may be the target. Cybercrime may harm someone's security or finances. There are many privacy concerns surrounding cybercrime when confidential information is intercepted or disclosed, lawfully or otherwise. Internationally, both governmental and non-state actors engage in cybercrimes, including espionage, financial theft, and other cross-border crimes. Cybercrimes crossing international borders and involving the actions of at least one nation-state are sometimes referred to as cyberwarfare. Warren Buffett describes cybercrime as the "number one problem with mankind" and said that cybercrime "poses real risks to humanity." A 2014 report sponsored by McAfee estimated that cybercrime resulted in $445 billion in annual damage ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |