|
Cyber-security Regulation
A cybersecurity regulation comprises directives that safeguard information technology and computer systems with the purpose of forcing companies and organizations to protect their systems and information from cyberattacks like viruses, worms, Trojan horses, phishing, denial of service (DOS) attacks, unauthorized access (stealing intellectual property or confidential information) and control system attacks. There are numerous measures available to prevent cyberattacks. Cybersecurity measures include firewalls, anti-virus software, intrusion detection and prevention systems, encryption, and login passwords. There have been attempts to improve cybersecurity through regulation and collaborative efforts between the government and the private sector to encourage voluntary improvements to cybersecurity. Industry regulators, including banking regulators, have taken notice of the risk from cybersecurity and have either begun or planned to begin to include cybersecurity as an aspect ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Technology
Information technology (IT) is the use of computers to create, process, store, retrieve, and exchange all kinds of Data (computing), data . and information. IT forms part of information and communications technology (ICT). An information technology system (IT system) is generally an information system, a communications system, or, more specifically speaking, a Computer, computer system — including all Computer hardware, hardware, software, and peripheral equipment — operated by a limited group of IT users. Although humans have been storing, retrieving, manipulating, and communicating information since the earliest writing systems were developed, the term ''information technology'' in its modern sense first appeared in a 1958 article published in the ''Harvard Business Review''; authors Harold Leavitt, Harold J. Leavitt and Thomas L. Whisler commented that "the new technology does not yet have a single established name. We shall call it information technology (IT)." Their ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Government
A government is the system or group of people governing an organized community, generally a state. In the case of its broad associative definition, government normally consists of legislature, executive, and judiciary. Government is a means by which organizational policies are enforced, as well as a mechanism for determining policy. In many countries, the government has a kind of constitution, a statement of its governing principles and philosophy. While all types of organizations have governance, the term ''government'' is often used more specifically to refer to the approximately 200 independent national governments and subsidiary organizations. The major types of political systems in the modern era are democracies, monarchies, and authoritarian and totalitarian regimes. Historically prevalent forms of government include monarchy, aristocracy, timocracy, oligarchy, democracy, theocracy, and tyranny. These forms are not always mutually exclusive, and mixe ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Critical Infrastructure Protection
Critical infrastructure protection (CIP) is a concept that relates to the preparedness and response to serious incidents that involve the critical infrastructure of a region or nation. The American Presidential directive PDD-63 of May 1998 set up a national program of "Critical Infrastructure Protection". In 2014 the NIST Cybersecurity Framework was published after further presidential directives. In Europe, the equivalent European Programme for Critical Infrastructure Protection (EPCIP) refers to the doctrine or specific programs created as a result of the European Commission's directive EU COM(2006) 786 which designates European critical infrastructure that, in case of fault, incident, or attack, could impact both the country where it is hosted and at least one other European Member State. Member states are obliged to adopt the 2006 directive into their national statutes. History of the U.S. CIP The U.S. CIP is a national program to ensure the security of vulnerable and i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Office Of Management And Budget
The Office of Management and Budget (OMB) is the largest office within the Executive Office of the President of the United States (EOP). OMB's most prominent function is to produce the president's budget, but it also examines agency programs, policies, and procedures to see whether they comply with the president's policies and coordinates inter-agency policy initiatives. Shalanda Young became OMB's acting director in March 2021, and was confirmed by the Senate in March 2022. History The Bureau of the Budget, OMB's predecessor, was established in 1921 as a part of the Department of the Treasury by the Budget and Accounting Act of 1921, which President Warren G. Harding signed into law. The Bureau of the Budget was moved to the Executive Office of the President in 1939 and was run by Harold D. Smith during the government's rapid expansion of spending during World War II. James L. Sundquist, a staffer at the Bureau of the Budget, called the relationship between the president a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Quality Act
The Information Quality Act (IQA) or Data Quality Act (DQA), passed through the United States Congress in Section 515 of the Consolidated Appropriations Act, 2001 (). Because the Act was a two-sentence rider in a spending bill, it had no name given in the actual legislation. The Government Accountability Office uses the name "Information Quality Act". IQA directs the Office of Management and Budget (OMB) to issue government-wide guidelines that "provide policy and procedural guidance to federal agencies for ensuring and maximizing the quality, objectivity, utility, and integrity of information (including statistical information) disseminated by Federal agencies". Other federal agencies are also required to publish their own guidelines for information quality and peer review agendas. Text of the IQA Consolidated Appropriations Act, 2001 Sec. 515 reads: (a) In General. – The Director of the Office of Management and Budget shall, by not later than September 30, 2001, and with p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bruce Schneier
Bruce Schneier (; born January 15, 1963) is an American cryptographer, computer security professional, privacy specialist, and writer. Schneier is a Lecturer in Public Policy at the Harvard Kennedy School and a Fellow at the Berkman Klein Center for Internet & Society as of November, 2013. He is a board member of the Electronic Frontier Foundation, Access Now, and The Tor Project; and an advisory board member of Electronic Privacy Information Center and VerifiedVoting.org. He is the author of several books on general security topics, computer security and cryptography and is a squid enthusiast. In 2015, Schneier received the EPIC Lifetime Achievement Award from Electronic Privacy Information Center. Early life Bruce Schneier is the son of Martin Schneier, a Brooklyn Supreme Court judge. He grew up in the Flatbush neighborhood of Brooklyn, New York, attending P.S. 139 and Hunter College High School. After receiving a physics bachelor's degree from the University of Rocheste ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Service Provider
An Internet service provider (ISP) is an organization that provides services for accessing, using, or participating in the Internet. ISPs can be organized in various forms, such as commercial, community-owned, non-profit, or otherwise privately owned. Internet services typically provided by ISPs can include Internet access, Internet transit, domain name registration, web hosting, Usenet service, and colocation. An ISP typically serves as the access point or the gateway that provides a user access to everything available on the Internet. Such a network can also be called as an eyeball network. History The Internet (originally ARPAnet) was developed as a network between government research laboratories and participating departments of universities. Other companies and organizations joined by direct connection to the backbone, or by arrangements through other connected companies, sometimes using dialup tools such as UUCP. By the late 1980s, a process was set in place ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Federal Information Security Management Act
The Federal Information Security Management Act of 2002 (FISMA, , ''et seq.'') is a United States federal law enacted in 2002 as Title III of the E-Government Act of 2002 (, ). The act recognized the importance of information security to the economic and national security interests of the United States. The act requires each federal agency to develop, document, and implement an agency-wide program to provide information security for the information and information systems that support the operations and assets of the agency, including those provided or managed by another agency, contractor, or other source. FISMA has brought attention within the federal government to cybersecurity and explicitly emphasized a "risk-based policy for cost-effective security." FISMA requires agency program officials, chief information officers, and inspectors general (IGs) to conduct annual reviews of the agency's information security program and report the results to Office of Management and Budge ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Homeland Security Act
The Homeland Security Act (HSA) of 2002, () was introduced in the aftermath of the September 11 attacks and subsequent mailings of anthrax spores. The HSA was cosponsored by 118 members of Congress. The act passed the U.S. Senate by a vote of 90–9, with one Senator not voting. It was signed into law by President George W. Bush in November 2002. HSA created the United States Department of Homeland Security and the new cabinet-level position of Secretary of Homeland Security. It is the largest federal government reorganization since the Department of Defense was created via the National Security Act of 1947 (as amended in 1949). It also includes many of the organizations under which the powers of the USA PATRIOT Act are exercised. Background The new department assumed a large number of services, offices and other organizations previously conducted in other departments, such as the Customs Service, Coast Guard, and U.S. Secret Service. It superseded, but did not replac ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Health Insurance Portability And Accountability Act
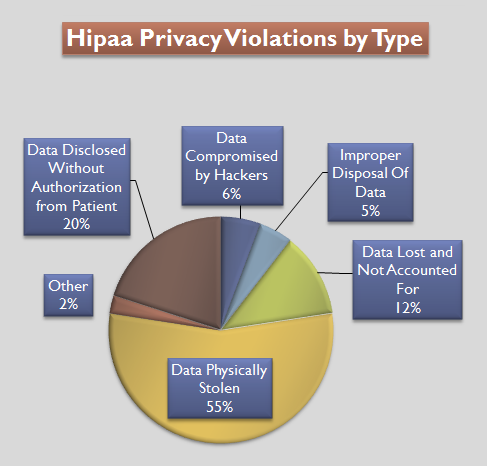
The Health Insurance Portability and Accountability Act of 1996 (HIPAA or the Kennedy– Kassebaum Act) is a United States Act of Congress enacted by the 104th United States Congress and signed into law by President Bill Clinton on August 21, 1996. It modernized the flow of healthcare information, stipulates how personally identifiable information maintained by the healthcare and healthcare insurance industries should be protected from fraud and theft, and addressed some limitations on healthcare insurance coverage. It generally prohibits healthcare providers and healthcare businesses, called ''covered entities'', from disclosing protected information to anyone other than a patient and the patient's authorized representatives without their consent. With limited exceptions, it does not restrict patients from receiving information about themselves. It does not prohibit patients from voluntarily sharing their health information however they choose, nor does it require confidentiali ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Federal Information Security Management Act Of 2002
The Federal Information Security Management Act of 2002 (FISMA, , ''et seq.'') is a United States federal law enacted in 2002 as Title III of the E-Government Act of 2002 (, ). The act recognized the importance of information security to the economic and national security interests of the United States. The act requires each federal agency to develop, document, and implement an agency-wide program to provide information security for the information and information systems that support the operations and assets of the agency, including those provided or managed by another agency, contractor, or other source. FISMA has brought attention within the federal government to cybersecurity and explicitly emphasized a "risk-based policy for cost-effective security." FISMA requires agency program officials, chief information officers, and inspectors general (IGs) to conduct annual reviews of the agency's information security program and report the results to Office of Management and Budg ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |