|
Cryptography Standards
There are a number of standards related to cryptography. Standard algorithms and protocols provide a focus for study; standards for popular applications attract a large amount of cryptanalysis. Encryption standards * Data Encryption Standard (DES, now obsolete) * Advanced Encryption Standard (AES) * RSA the original public key algorithm * OpenPGP Hash standards * MD5 128-bit (obsolete) * SHA-1 160-bit (obsolete) * SHA-2 available in 224, 256, 384, and 512-bit variants * HMAC keyed hash * PBKDF2 Key derivation function (RFC 2898) Digital signature standards * Digital Signature Standard (DSS), based on the Digital Signature Algorithm (DSA) * RSA * Elliptic Curve DSA Public-key infrastructure (PKI) standards * X.509 Public Key Certificates Wireless Standards * Wired Equivalent Privacy (WEP), severely flawed and superseded by WPA * Wi-Fi Protected Access (WPA) better than WEP, a 'pre-standard' partial version of 802.11i * 802.11i a.k.a. WPA2, uses AES and other improvements o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Standardization
Standardization (American English) or standardisation (British English) is the process of implementing and developing technical standards based on the consensus of different parties that include firms, users, interest groups, standards organizations and governments. Standardization can help maximize compatibility, interoperability, safety, repeatability, efficiency, and quality. It can also facilitate a normalization of formerly custom processes. In social sciences, including economics, the idea of ''standardization'' is close to the solution for a coordination problem, a situation in which all parties can realize mutual gains, but only by making mutually consistent decisions. Divergent national standards impose costs on consumers and can be a form of non-tariff trade barrier. History Early examples Standard weights and measures were developed by the Indus Valley civilization.Iwata, Shigeo (2008), "Weights and Measures in the Indus Valley", ''Encyclopaedia of the History ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Institute Of Standards And Technology
The National Institute of Standards and Technology (NIST) is an agency of the United States Department of Commerce whose mission is to promote American innovation and industrial competitiveness. NIST's activities are organized into Outline of physical science, physical science laboratory programs that include Nanotechnology, nanoscale science and technology, engineering, information technology, neutron research, material measurement, and physical measurement. From 1901 to 1988, the agency was named the National Bureau of Standards. History Background The Articles of Confederation, ratified by the colonies in 1781, provided: The United States in Congress assembled shall also have the sole and exclusive right and power of regulating the alloy and value of coin struck by their own authority, or by that of the respective states—fixing the standards of weights and measures throughout the United States. Article 1, section 8, of the Constitution of the United States, ratified i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Tempest (codename)
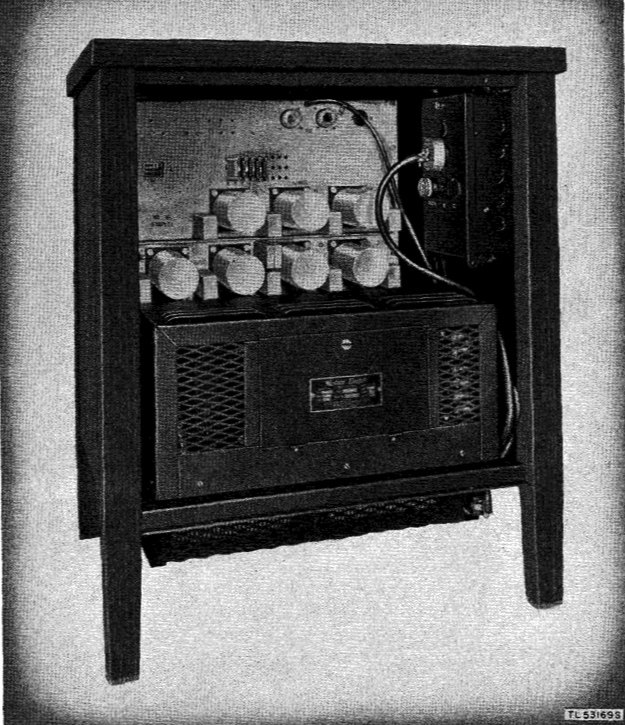
TEMPEST is a codename, not an acronym under the U.S. National Security Agency specification and a NATO certification referring to spying on information systems through leaking emanations, including unintentional radio or electrical signals, sounds, and vibrations. TEMPEST covers both methods to spy upon others and how to shield equipment against such spying. The protection efforts are also known as emission security (EMSEC), which is a subset of communications security (COMSEC). The reception methods fall under the umbrella of radiofrequency MASINT. The NSA methods for spying on computer emissions are classified, but some of the protection standards have been released by either the NSA or the Department of Defense. Protecting equipment from spying is done with distance, shielding, filtering, and masking. The TEMPEST standards mandate elements such as equipment distance from walls, amount of shielding in buildings and equipment, and distance separating wires carrying classified v ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
STU-III
STU-III (Secure Telephone Unit - third generation) is a family of secure telephones introduced in 1987 by the NSA for use by the United States government, its contractors, and its allies. STU-III desk units look much like typical office telephones, plug into a standard telephone wall jack and can make calls to any ordinary phone user (with such calls receiving no special protection, however). When a call is placed to another STU-III unit that is properly set up, one caller can ask the other to initiate secure transmission. They then press a button on their telephones and, after a 15-second delay, their call is encrypted to prevent eavesdropping. There are portable and militarized versions and most STU-IIIs contained an internal modem and RS-232 port for data and fax transmission. Vendors were AT&T (later transferred to Lucent Technologies), RCA (now L-3 Communications, East) and Motorola. STU-III are no longer in service with the U.S. Government, with the last cryptographic ke ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Terminal Equipment
Secure Terminal Equipment (STE) is the U.S. government's current (), encrypted telephone communications system for wired or "landline" communications. STE is designed to use ISDN telephone lines which offer higher speeds of up to 128 kbit/s and are all digital. The greater bandwidth allows higher quality voice and can also be utilized for data and fax transmission through a built-in RS-232 port. STE is intended to replace the older STU-III office system and the KY-68 tactical system. STE sets are backwards compatible with STU-III phones, but not with KY-68 sets. STE sets look like ordinary high-end office desk telephones and can place unsecured calls to anywhere on the public switched telephone network (PSTN), as well as secured calls on it via the phone's backwards compatible STU-III mode. There is a PC Card slot in the STE that allows a Fortezza Plus ( KOV-14) Crypto Card or KSV-21 Enhanced Crypto Card to be inserted. When an NSA-configured Crypto Card is present, sec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
PC Card
PC Card is a technical standard specifying an expansion card interface for laptops and personal digital assistants, PDAs. The PCMCIA originally introduced the 16-bit Industry Standard Architecture, ISA-based PCMCIA Card in 1990, but renamed it to PC Card in March 1995 to avoid confusion with the name of the organization. The CardBus PC Card was introduced as a 32-bit version of the original PC Card, based on the Peripheral Component Interconnect, PCI specification. CardBus slots are Backward compatibility, backwards compatible, but older slots are not Forward compatibility, forward compatible with CardBus cards. Although originally designed as a standard for memory-expansion cards for computer storage, the existence of a usable general standard for notebook peripherals led to the development of many kinds of devices including network cards, modems, and hard disks. The PC Card port has been superseded by the ExpressCard interface since 2003, which was also initially developed by t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fortezza
Fortezza is an information security system that uses the Fortezza Crypto Card, a PC Card-based security token. It was developed for the U.S. government's Clipper chip project and has been used by the U.S. Government in various applications. Each individual who is authorized to see protected information is issued a ''Fortezza card'' that stores private keys and other data needed to gain access. It contains an NSA approved security microprocessor called '' Capstone'' ( MYK-80) that implements the Skipjack encryption algorithm. The original Fortezza card (KOV-8) is a Type 2 product which means it cannot be used for classified information. The most widely used Type 1 encryption card is the KOV-12 Fortezza card which is used extensively for the Defense Message System (DMS). The KOV-12 is cleared up to TOP SECRET/SCI. A later version, called KOV-14 or Fortezza Plus, uses a Krypton microprocessor that implements stronger, Type 1 encryption and may be used for information clas ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
FNBDT
The Secure Communications Interoperability Protocol (SCIP) is a US standard for secure voice and data communication, focircuit-switchedone-to-one connections, not packet-switched networks. SCIP derived from the US Government Future Narrowband Digital Terminal (FNBDT) project. SCIP supports a number of different modes, including national and multinational modes which employ different cryptography. Many nations and industries develop SCIP devices to support the multinational and national modes of SCIP. SCIP has to operate over the wide variety of communications systems, including commercial land line telephone, military radios, communication satellites, Voice over IP and the several different cellular telephone standards. Therefore, it was designed to make no assumptions about the underlying channel other than a minimum bandwidth of 2400 Hz. It is similar to a dial-up modem in that once a connection is made, two SCIP phones first negotiate the parameters they need and then comm ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EKMS
The Electronic Key Management System (EKMS) is a United States National Security Agency led program responsible for Communications Security ( COMSEC) key management, accounting, and distribution. Specifically, EKMS generates and distributes electronic key material for all NSA encryption systems whose keys are loaded using standard fill devices, and directs the distribution of NSA produced key material. Additionally, EKMS performs account registration, privilege management, ordering, distribution, and accounting to direct the management and distribution of physical COMSEC material for the services. The common EKMS components and standards facilitate interoperability and commonality among the armed services and civilian agencies. Key Management Infrastructure (KMI) replaces EKMS. Reasons for development The primary reason for the development of EKMS centers on the security and logistics problems that plagued the COMSEC Material Control System (CMCS),{{cite web, url=http://apps ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Public Key Cryptography
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public key and a corresponding private key. Key pairs are generated with cryptographic algorithms based on mathematical problems termed one-way functions. Security of public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. There are many kinds of public-key cryptosystems, with different security goals, including digital signature, Diffie–Hellman key exchange, public-key key encapsulation, and public-key encryption. Public key algorithms are fundamental security primitives in modern cryptosystems, including applications and protocols that offer assurance of the confidentiality and authenticity of electronic communications and data storage. They underpin numerous Internet standards, such as Transport Layer Security (TLS), SSH, S/MIME, and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Local Area Network
A local area network (LAN) is a computer network that interconnects computers within a limited area such as a residence, campus, or building, and has its network equipment and interconnects locally managed. LANs facilitate the distribution of data and sharing network devices, such as printers. The LAN contrasts the wide area network (WAN), which not only covers a larger geographic distance, but also generally involves Leased line, leased telecommunication circuits or Internet links. An even greater contrast is the Internet, which is a system of globally connected business and personal computers. Ethernet and Wi-Fi are the two most common technologies used for local area networks; historical network technologies include ARCNET, Token Ring, and LocalTalk. Cabling Most wired network infrastructures utilize Category 5 cable, Category 5 or Category 6 cable, Category 6 twisted pair cabling with RJ45 (telecommunications), RJ45 compatible terminations. This medium provides physical ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an Logical assertion, assertion, such as the Digital identity, identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. Authentication is relevant to multiple fields. In art, antiques, and anthropology, a common problem is verifying that a given artifact was produced by a certain person, or in a certain place (i.e. to assert that it is not counterfeit), or in a given period of history (e.g. by determining the age via carbon dating). In computer science, verifying a user's identity is often required to allow access to confidential data or systems. It might involve validating personal identity documents. In art, antiques and anthropology Authentication can be considered to be of three types: The ''first'' type of authentication is accep ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |