|
Cascade (computer Virus)
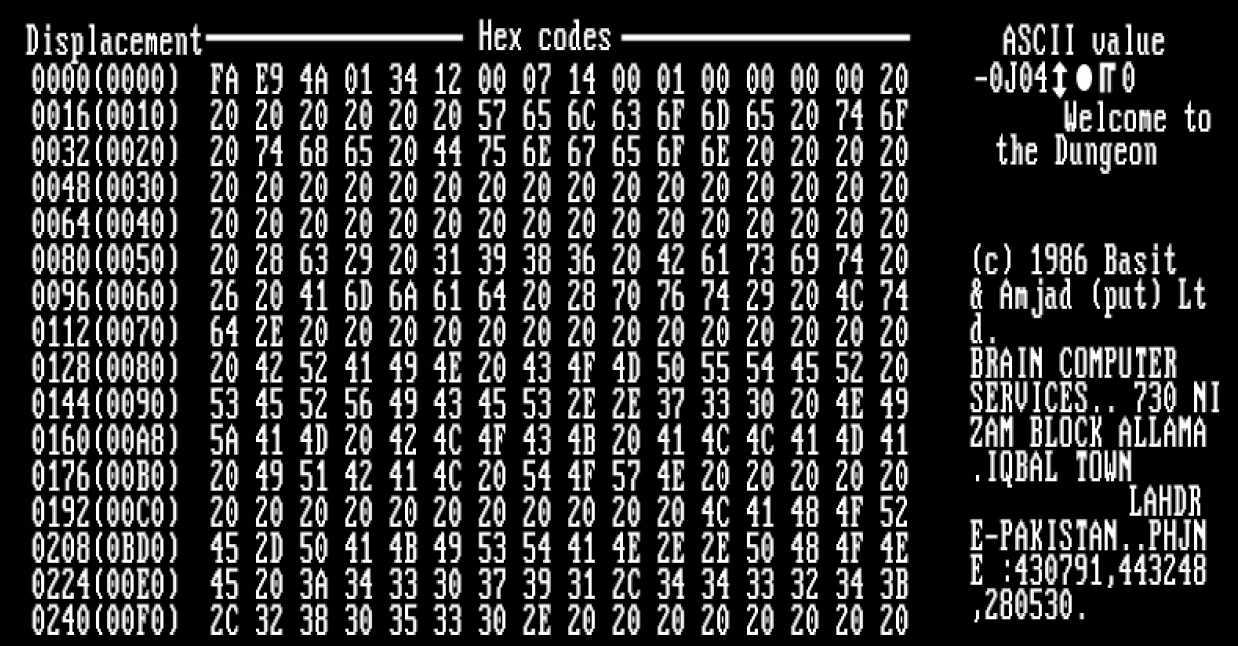
The Cascade virus (also known as ''Herbstlaub'' in Germany) is a prominent computer virus that was a resident written in assembly language, that was widespread in the 1980s and early 1990s. It infected .COM files and had the effect of making text on the screen fall (or cascade) down and form a heap at the bottom of the screen. It was notable for using an encryption In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ... algorithm to avoid being detected. However, one could see that infected files had their size increased by 1701 or 1704 bytes. In response, IBM developed its own antivirus software. The virus has a number of variants. Cascade-17Y4, which is reported to have originated in Yugoslavia, is almost identical to the most common 1704 byte variant. One byte has been changed, pr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. A computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks. Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can inclu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Assembly Language
In computer programming, assembly language (or assembler language, or symbolic machine code), often referred to simply as Assembly and commonly abbreviated as ASM or asm, is any low-level programming language with a very strong correspondence between the instructions in the language and the architecture's machine code instructions. Assembly language usually has one statement per machine instruction (1:1), but constants, comments, assembler directives, symbolic labels of, e.g., memory locations, registers, and macros are generally also supported. The first assembly code in which a language is used to represent machine code instructions is found in Kathleen and Andrew Donald Booth's 1947 work, ''Coding for A.R.C.''. Assembly code is converted into executable machine code by a utility program referred to as an ''assembler''. The term "assembler" is generally attributed to Wilkes, Wheeler and Gill in their 1951 book ''The Preparation of Programs for an Electronic Digital Com ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IBM Personal Computer
The IBM Personal Computer (model 5150, commonly known as the IBM PC) is the first microcomputer released in the IBM PC model line and the basis for the IBM PC compatible de facto standard. Released on August 12, 1981, it was created by a team of engineers and designers directed by Don Estridge in Boca Raton, Florida. The machine was based on open architecture and third-party peripherals. Over time, expansion cards and software technology increased to support it. The PC had a influence of the IBM PC on the personal computer market, substantial influence on the personal computer market. The specifications of the IBM PC became one of the most popular computer design standards in the world. The only significant competition it faced from a non-compatible platform throughout the 1980s was from the Apple Macintosh product line. The majority of modern personal computers are distant descendants of the IBM PC. History Prior to the 1980s, IBM had largely been known as a provider of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IBM PC Compatibles
IBM PC compatible computers are similar to the original IBM PC, XT, and AT, all from computer giant IBM, that are able to use the same software and expansion cards. Such computers were referred to as PC clones, IBM clones or IBM PC clones. The term "IBM PC compatible" is now a historical description only, since IBM no longer sells personal computers after it sold its personal computer division in 2005 to Chinese technology company Lenovo. The designation "PC", as used in much of personal computer history, has not meant "personal computer" generally, but rather an x86 computer capable of running the same software that a contemporary IBM PC could. The term was initially in contrast to the variety of home computer systems available in the early 1980s, such as the Apple II, TRS-80, and Commodore 64. Later, the term was primarily used in contrast to Apple's Macintosh computers. These "clones" duplicated almost all the significant features of the original IBM PC architectures. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. A computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks. Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can inclu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Assembly Language
In computer programming, assembly language (or assembler language, or symbolic machine code), often referred to simply as Assembly and commonly abbreviated as ASM or asm, is any low-level programming language with a very strong correspondence between the instructions in the language and the architecture's machine code instructions. Assembly language usually has one statement per machine instruction (1:1), but constants, comments, assembler directives, symbolic labels of, e.g., memory locations, registers, and macros are generally also supported. The first assembly code in which a language is used to represent machine code instructions is found in Kathleen and Andrew Donald Booth's 1947 work, ''Coding for A.R.C.''. Assembly code is converted into executable machine code by a utility program referred to as an ''assembler''. The term "assembler" is generally attributed to Wilkes, Wheeler and Gill in their 1951 book ''The Preparation of Programs for an Electronic Digital Com ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
COM File
A COM file is a type of simple executable file. On the Digital Equipment Corporation (DEC) VAX operating systems of the 1970s, .COM was used as a filename extension for text files containing commands to be issued to the operating system (similar to a batch file). With the introduction of Digital Research's CP/M (a microcomputer operating system), the type of files commonly associated with COM extension changed to that of executable files. This convention was later carried over to DOS. Even when complemented by the more general .exe, EXE file format for executables, the compact COM files remained viable and frequently used under DOS. The .COM file name extension has no relation to the .com (for "commercial") top-level Internet domain name. However, this similarity in name has been exploited by malware writers. DOS binary format The COM format is the original binary executable format used in CP/M (including SCP (operating system), SCP and MSX-DOS) as well as DOS. It is very sim ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decipher a ciphertext back to plaintext and access the original information. Encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often used in military ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect from other computer threats. In particular, modern antivirus software can protect users from malicious browser helper objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraud tools, adware, and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, advanced persistent threat (APT), and botnet DDoS attacks. History 1949–1980 period (pre-antivirus days) Although the roots of the computer ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
DOS File Viruses
DOS is shorthand for the MS-DOS and IBM PC DOS family of operating systems. DOS may also refer to: Computing * Data over signalling (DoS), multiplexing data onto a signalling channel * Denial-of-service attack (DoS), an attack on a communications network * Disk operating system ** List of disk operating systems, Apple DOS, Atari DOS, DOS/360, etc. * Distributed operating system Music Albums * ''Dos'' (Altered State album) * ''Dos'' (Dos album) * ''Dos'' (Fanny Lú album) * ''Dos'' (Gerardo album) * ''Dos'' (Malo album), 1972 * ''Dos'' (Myriam Hernández album), 1989 * ''Dos'', album by Wooden Shjips, 2009 * ''¡Dos!'', album by Green Day Other uses in music * Dos (band), an American band * DOS (concert), by Filipino singer Daniel Padilla Organisations * Democratic Opposition of Serbia, a former political alliance * Department of Space, India * Deutscher Olympischer Sportbund * Directorate of Overseas Surveys, UK 1957–1984 *Dominus Obsequious Sororium, within cult NXIV ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |