|
Blue Team (computer Security)
A blue team is a group of individuals who perform an analysis of information systems to ensure security, identify security flaws, verify the effectiveness of each security measure, and to make certain all security measures will continue to be effective after implementation. History As part of the United States computer security defense initiative, red teams were developed to exploit other malicious entities that would do them harm. As a result, blue teams were developed to design defensive measures against such red team activities. Incident response If an incident does occur within the organization, the blue team will perform the following six steps to handle the situation: #Preparation #Identification #Containment #Eradication #Recovery #Lessons learned Operating system hardening In preparation for a computer security incident, the blue team will perform hardening techniques on all operating systems throughout the organization. Perimeter defense The blue team must always be min ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Systems
An information system (IS) is a formal, sociotechnical, organizational system designed to collect, process, information storage, store, and information distribution, distribute information. From a sociotechnical perspective, information systems are composed by four components: task, people, structure (or roles), and technology. Information systems can be defined as an integration of components for collection, storage and data processing, processing of data of which the data is used to provide information, contribute to knowledge as well as digital products that facilitate decision making. A computer information system is a system that is composed of people and computers that processes or interprets information. The term is also sometimes used to simply refer to a computer, computer system with software installed. "Information systems" is also an academic field study about systems with a specific reference to information and the complementary networks of computer hardware and soft ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
White Hat (computer Security)
A white hat (or a white-hat hacker, a whitehat) is an ethical security hacker. Ethical hacking is a term meant to imply a broader category than just penetration testing. Under the owner's consent, white-hat hackers aim to identify any vulnerabilities the current system has. The white hat is contrasted with the black hat, a malicious hacker; this definitional dichotomy comes from Western films, where heroic and antagonistic cowboys might traditionally wear a white and a black hat, respectively. There is a third kind of hacker known as a grey hat who hacks with good intentions but at times without permission. White-hat hackers may also work in teams called " sneakers and/or hacker clubs", red teams, or tiger teams. History One of the first instances of an ethical hack being used was a "security evaluation" conducted by the United States Air Force, in which the Multics operating systems were tested for "potential use as a two-level (secret/top secret) system." The evaluation deter ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Vulnerability Management
Vulnerability management is the "cyclical practice of identifying, classifying, prioritizing, remediating, and mitigating" software vulnerabilities. Vulnerability management is integral to computer security and network security, and must not be confused with vulnerability assessment. Vulnerabilities can be discovered with a vulnerability scanner, which analyzes a computer system in search of known vulnerabilities,Anna-Maija Juuso and Ari Takanen ''Unknown Vulnerability Management'', Codenomicon whitepaper, October 201 such as open ports, insecure software configurations, and susceptibility to malware infections. They may also be identified by consulting public sources, such as NVD, or subscribing to a commercial vulnerability alerting service such as Symantec's DeepSight Vulnerability Datafeed or Accenture's Vulnerability Intelligence Service. Unknown vulnerabilities, such as a zero-day, may be found with fuzz testing. Fuzzy testing can identify certain kinds of vulnerabiliti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of Digital Forensics Tools
During the 1980s, most digital forensic investigations consisted of "live analysis", examining digital media directly using non-specialist tools. In the 1990s, several freeware and other proprietary tools (both hardware and software) were created to allow investigations to take place without modifying media. This first set of tools mainly focused on computer forensics, although in recent years similar tools have evolved for the field of mobile device forensics. This list includes notable examples of digital forensic tools. Forensics-focused operating systems Debian-based * Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing, formerly known as BackTrack. * Parrot Security OS is a cloud-oriented Linux distribution based on Debian and designed to perform security and penetration tests, do forensic analysis, or act in anonymity. It uses the MATE Desktop Environment, Linux Kernel 4.6 or higher and it is available as a live li ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyber Threat Intelligence
Cyber threat intelligence (CTI) is knowledge, skills and experience-based information concerning the occurrence and assessment of both cyber and physical threats and threat actors that is intended to help mitigate potential attacks and harmful events occurring in cyberspace. Cyber threat intelligence sources include open source intelligence, social media intelligence, human Intelligence, technical intelligence, device log files, forensically acquired data or intelligence from the internet traffic and data derived for the deep and dark web. In recent years, threat intelligence has become a crucial part of companies' cyber security strategy since it allows companies to be more proactive in their approach and determine which threats represent the greatest risks to a business. This puts companies on a more proactive front - actively trying to find their vulnerabilities and prevents hacks before they happen. This method is gaining importance in recent years since, as IBM estimates, the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
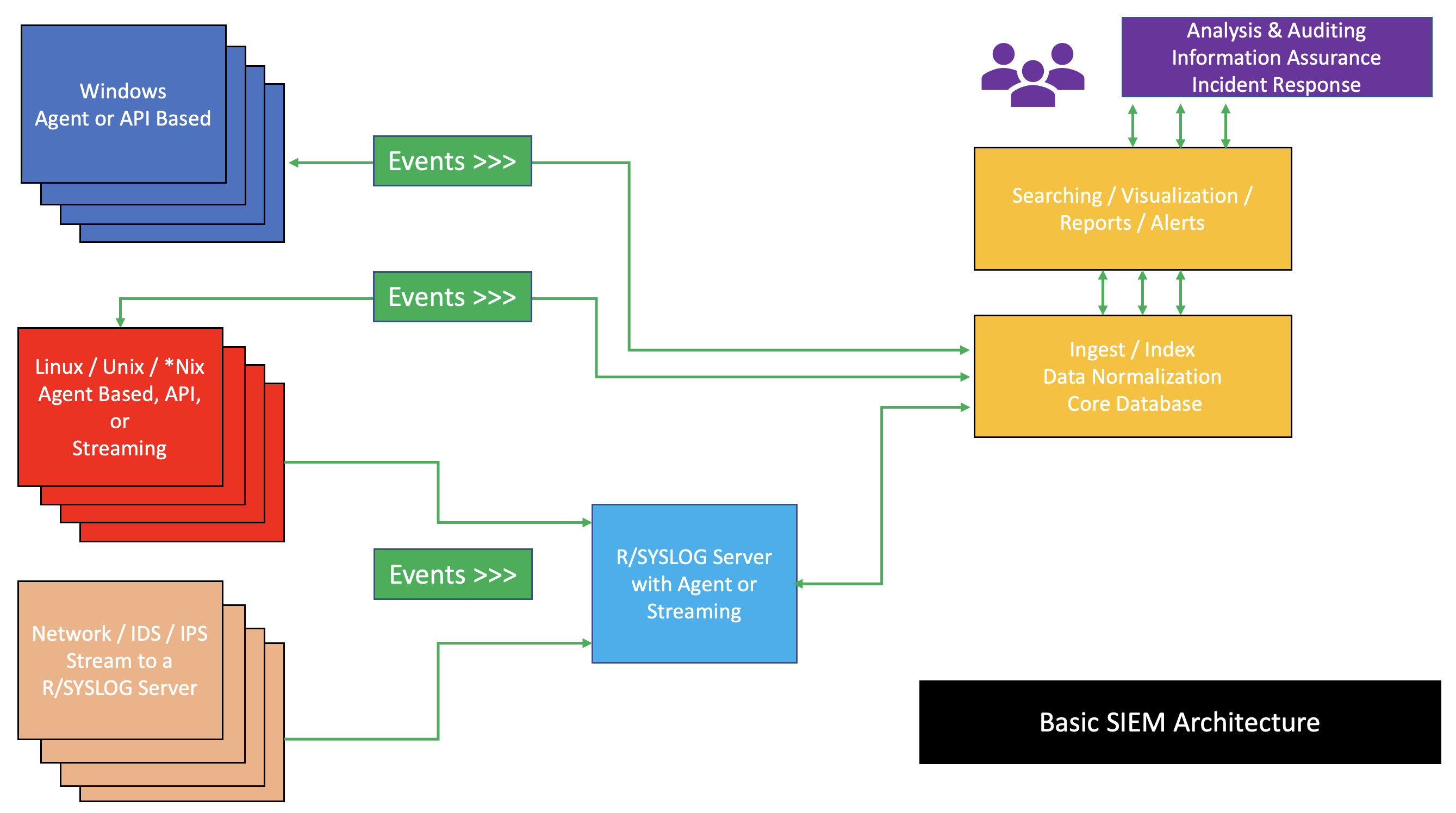
Security Information And Event Management
Security information and event management (SIEM) is a field within the field of computer security, where software products and services combine security information management (SIM) and security event management (SEM). They provide real-time analysis of security alerts generated by applications and network hardware. Vendors sell SIEM as software, as appliances, or as managed services; these products are also used to log security data and generate reports for compliance purposes. The term and the initialism SIEM was coined by Mark Nicolett and Amrit Williams of Gartner in 2005. History Monitoring system logs has grown more prevalent as complex cyber-attacks force compliance and regulatory mechanisms to mandate logging security controls within a Risk Management Framework. Logging levels of a system started with the primary function of troubleshooting system errors or debugging code compiled and run. As operating systems and networks have increased in complexity, so has the event ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Splunk
Splunk Inc. is an American software company based in San Francisco, California, that produces software for searching, monitoring, and analyzing machine-generated data via a Web-style interface. Its software helps capture, index and correlate real-time data in a searchable repository, from which it can generate graphs, reports, alerts, dashboards and visualizations. Splunk uses machine data for identifying data patterns, providing metrics, diagnosing problems and providing intelligence for business operations. Splunk is a horizontal technology used for application management, security and compliance, as well as business and web analytics. History Founding & early years Michael Baum, Rob Das and Erik Swan co-founded Splunk Inc in 2003. Venture firms August Capital, Sevin Rosen, Ignition Partners and JK&B Capital backed the company. By 2007 Splunk had raised . It became profitable in 2009. In 2012 Splunk had its initial public offering, trading under NASDAQ symbol SPLK. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SolarWinds
SolarWinds Corporation is an American company that develops software for businesses to help manage their networks, systems, and information technology infrastructure. It is headquartered in Austin, Texas, with sales and product development offices in a number of locations in the United States and several other countries. The company was publicly traded from May 2009 until the end of 2015, and again from October 2018. It has also acquired a number of other companies, some of which it still operates under their original names, including Pingdom, Papertrail and Loggly. It had about 300,000 customers as of December 2020, including nearly all ''Fortune'' 500 companies and numerous federal agencies. A SolarWinds product, Orion, used by about 33,000 public and private sector customers, was the focus of a large-scale attack disclosed in December 2020. The attack persisted undetected for months in 2020, and additional details about the breadth and depth of compromised systems continue ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Rapid7
The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. It is owned by Boston, Massachusetts-based security company Rapid7. Its best-known sub-project is the open-source Metasploit Framework, a tool for developing and executing exploit code against a remote target machine. Other important sub-projects include the Opcode Database, shellcode archive and related research. The Metasploit Project includes anti-forensic and evasion tools, some of which are built into the Metasploit Framework. Metasploit is pre-installed in the Kali Linux operating system. History Metasploit was created by H. D. Moore in 2003 as a portable network tool using Perl. By 2007, the Metasploit Framework had been completely rewritten in Ruby. On October 21, 2009, the Metasploit Project announced that it had been acquired by Rapid7, a security company that provides unified vulnerability ma ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Netwitness
NetWitness is a network security company that provides real-time network forensics automated threat detection, response, and analysis solutions. The company is based in Bedford, Massachusetts. In 2011, NetWitness was acquired by EMC Corporation and in 2020 was acquired by Symphony Technology Group as a stand alone business unit, part of RSA Security. History In the mid-1990s the NetWitness technology was established by CTX Corporation, a Washington D.C. based system integrator. The technology, initially chartered as a US Government research project, was created to help analysts better understand large volumes of captured network data for various types of investigations. CTX Corporation was subsequently acquired by ManTech International Corporation () in December 2002. At Mantech, the technology was further developed to aid Federal Law Enforcement in criminal investigations and support professional service engagements for the Federal Government and commercial organizations. In N ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |