|
BackTrack
BackTrack was a Linux distribution that focused on security, based on the Knoppix Linux distribution aimed at digital forensics and penetration testing use. In March 2013, the Offensive Security team rebuilt BackTrack around the Debian distribution and released it under the name Kali Linux. History The BackTrack distribution originated from the merger of two formerly competing distributions which focused on penetration testing: * ''WHAX'': a Slax-based Linux distribution developed by Mati Aharoni, a security consultant. Earlier versions of WHAX were called ''Whoppix'' and were based on Knoppix. * ''Auditor Security Collection'': a Live CD based on Knoppix developed by ''Max Moser'' which included over 300 tools organized in a user-friendly hierarchy. On January 9, 2010, BackTrack 4 improved hardware support, and added official FluxBox support. The overlap with Auditor and WHAX in purpose and in collection of tools partly led to the merger. The overlap was done based on Ubuntu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
BackTrack 5 R1
BackTrack was a Linux distribution that focused on security, based on the Knoppix Linux distribution aimed at digital forensics and penetration testing use. In March 2013, the Offensive Security team rebuilt BackTrack around the Debian distribution and released it under the name Kali Linux. History The BackTrack distribution originated from the merger of two formerly competing distributions which focused on penetration testing: * ''WHAX'': a Slax-based Linux distribution developed by Mati Aharoni, a security consultant. Earlier versions of WHAX were called ''Whoppix'' and were based on Knoppix. * ''Auditor Security Collection'': a Live CD based on Knoppix developed by ''Max Moser'' which included over 300 tools organized in a user-friendly hierarchy. On January 9, 2010, BackTrack 4 improved hardware support, and added official FluxBox support. The overlap with Auditor and WHAX in purpose and in collection of tools partly led to the merger. The overlap was done based on Ubun ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
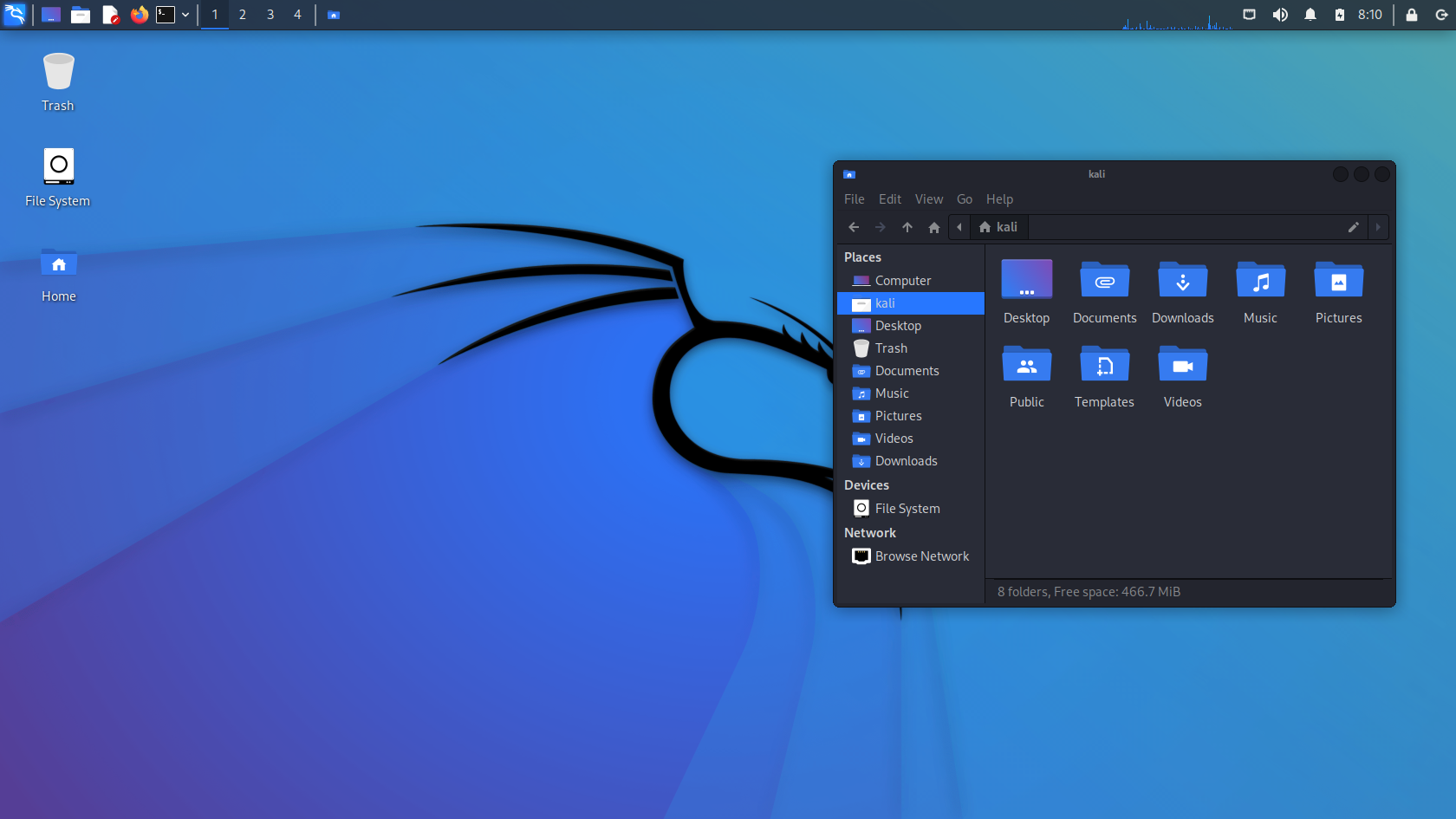
Kali Linux
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security. Kali Linux has around 600 penetration-testing programs (tools), including Armitage (a graphical cyber attack management tool), Nmap (a port scanner), Wireshark (a packet analyzer), metasploit (penetration testing framework), John the Ripper (a password cracker), sqlmap (automatic SQL injection and database takeover tool), Aircrack-ng (a software suite for penetration-testing wireless LANs), Burp suite and OWASP ZAP web application security scanners, etc. It was developed by Mati Aharoni and Devon Kearns of Offensive Security through the rewrite of BackTrack, their previous information security testing Linux distribution based on Knoppix. The name was inspired by the Hindu goddess Kali. Kali Linux is based on the Debian ''Testing'' branch. Most packages Kali uses are imported from the Debian repositories. Kali Linux's pop ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Knoppix
KNOPPIX ( ) is an operating system based on Debian designed to be run directly from a CD / DVD (Live CD) or a USB flash drive (Live USB), one of the first live operating system distributions (just after Yggdrasil Linux). Knoppix was developed by, and named after, Linux consultant Klaus Knopper. When starting a program, it is loaded from the removable medium and decompressed into a RAM drive. The decompression is transparent and on-the-fly. Although KNOPPIX is primarily designed to be used as a Live CD, it can also be installed on a hard disk like a typical operating system. Computers that support booting from USB devices can load KNOPPIX from a live USB flash drive or memory card. There are two main editions: the traditional compact-disc (700 megabytes) edition and the DVD (4.7 gigabytes) "Maxi" edition. The CD edition had not been updated since June 2013 until recently. As of version 9.1, CD images are being released once again. Each main edition has two language-specific edi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Packet Injection
Packet injection (also known as forging packets or spoofing packets) in computer networking, is the process of interfering with an established network connection by means of constructing packets to appear as if they are part of the normal communication stream. The packet injection process allows an unknown third party to disrupt or intercept packets from the consenting parties that are communicating, which can lead to degradation or blockage of users' ability to utilize certain network services or protocols. Packet injection is commonly used in man-in-the-middle attacks and denial-of-service attacks. Capabilities By utilizing raw sockets, NDIS function calls, or direct access to a network adapter kernel mode driver, arbitrary packets can be constructed and injected into a computer network. These arbitrary packets can be constructed from any type of packet protocol ( ICMP, TCP, UDP, and others) since there is full control over the packet header while the packet is being assemb ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Penetration Test
A penetration test, colloquially known as a pen test or ethical hacking, is an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system; this is not to be confused with a vulnerability assessment. The test is performed to identify weaknesses (also referred to as vulnerabilities), including the potential for unauthorized parties to gain access to the system's features and data, as well as strengths, enabling a full risk assessment to be completed. The process typically identifies the target systems and a particular goal, then reviews available information and undertakes various means to attain that goal. A penetration test target may be a white box (about which background and system information are provided in advance to the tester) or a black box (about which only basic information—if any—other than the company name is provided). A gray box penetration test is a combination of the two (where limited knowledge of the target is sh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Aircrack-ng
Aircrack-ng is a network software suite consisting of a detector, packet sniffer, WEP and WPA/WPA2-PSK cracker and analysis tool for 802.11 wireless LANs. It works with any wireless network interface controller whose driver supports raw monitoring mode and can sniff 802.11a, 802.11b and 802.11g traffic. The program runs under Linux, FreeBSD, macOS, OpenBSD, and Windows; the Linux version is packaged for OpenWrt and has also been ported to the Android, Zaurus PDA and Maemo platforms; and a proof of concept port has been made to the iPhone. In April 2007 a team at the Darmstadt University of Technology in Germany developed a new attack method based on a paper released on the RC4 cipher by Adi Shamir. This new attack, named 'PTW', decreases the number of initialization vectors or IVs needed to decrypt a WEP key and has been included in the aircrack-ng suite since the 0.9 release. Aircrack-ng is a fork of the original Aircrack project. It can be found as a preinstalled tool in m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kismet (software)
Kismet is a network detector, packet sniffer, and intrusion detection system for 802.11 wireless LANs. Kismet will work with any wireless card which supports raw monitoring mode, and can sniff 802.11a, 802.11b, 802.11g, and 802.11n traffic. The program runs under Linux, FreeBSD, NetBSD, OpenBSD, and macOS. The client can also run on Microsoft Windows, although, aside from external drones (see below), there's only one supported wireless hardware available as packet source. Distributed under the GNU General Public License, Kismet is free software. Features Kismet differs from other wireless network detectors in working passively. Namely, without sending any loggable packets, it is able to detect the presence of both wireless access points and wireless clients, and to associate them with each other. It is also the most widely used and up to date open source wireless monitoring tool. Kismet also includes basic wireless IDS features such as detecting active wireless sniffing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Nmap
Nmap (Network Mapper) is a network scanner created by Gordon Lyon (also known by his pseudonym ''Fyodor Vaskovich''). Nmap is used to discover hosts and services on a computer network by sending packets and analyzing the responses. Nmap provides a number of features for probing computer networks, including host discovery and service and operating system detection. These features are extensible by scripts that provide more advanced service detection, vulnerability detection, and other features. Nmap can adapt to network conditions including latency and congestion during a scan. Nmap started as a Linux utility and was ported to other systems including Windows, macOS, and BSD. It is most popular on Linux, followed by Windows. Features Nmap features include: * Host discovery – Identifying hosts on a network. For example, listing the hosts that respond to TCP and/or ICMP requests or have a particular port open. * Port scanning – Enumerating the open ports on target hosts. * V ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wi-Fi Protected Setup
Wi-Fi Protected Setup (WPS; originally, Wi-Fi Simple Config) is a network security standard to create a secure wireless home network. Created by Cisco and introduced in 2006, the point of the protocol is to allow home users who know little of wireless security and may be intimidated by the available security options to set up Wi-Fi Protected Access, as well as making it easy to add new devices to an existing network without entering long passphrases. Wi-Fi Protected Setup allows the owner of Wi-Fi privileges to block other users from using their household Wi-Fi. The owner can also allow people to use Wi-Fi. This can be changed by pressing the WPS button on the home router. A major security flaw was revealed in December 2011 that affects wireless routers with the WPS PIN feature, which most recent models have enabled by default. The flaw allows a remote attacker to recover the WPS PIN in a few hours with a brute-force attack and, with the WPS PIN, the network's WPA/WPA2 pre-shar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mati Aharoni
Mati may refer to: Geography *Mati, Davao Oriental, Philippines, a city **Roman Catholic Diocese of Mati ** Mati Protected Landscape, a protected area in Davao Oriental, Philippines **Mati Airport, Davao Oriental, Philippines *Mati, a barangay in San Miguel, Zamboanga del Sur, Philippines * Mati, Greece, a holiday resort village on the east coast of the Attica region, 29 kilometres east of Athens *Mati, Nepal, a village development committee in Dolakha District, Janakpur Zone *Mati, Lucknow, a village in Uttar Pradesh, India * Mat (river), a river in Albania * Mat (region), a region in Albania People * Mati (given name) * Fred Mbiti Gideon Mati (), Kenyan politician Other uses * Ma-Ti, character from the ''Captain Planet and the Planeteers'' TV series *Moscow State Aviation Technological University (MATI) * Mati Community College, Davao Oriental, Philippines *''Mati'', original title of the 1977 film '' Beyond Reason'' See also * Matti (other) * Matis (other) ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Monitor Mode
Monitor or monitor may refer to: Places * Monitor, Alberta * Monitor, Indiana, town in the United States * Monitor, Kentucky * Monitor, Oregon, unincorporated community in the United States * Monitor, Washington * Monitor, Logan County, West Virginia * Monitor, Monroe County, West Virginia * Loope, California, formerly Monitor Arts, entertainment, and media Fictional characters * Monitor (Mar Novu), a DC comics character * Monitors (DC Comics), a group of fictional comic book characters, who appear in books published by DC Comics Periodicals * ''Monitor'' (magazine), a weekly newsmagazine published in Podgorica, Montenegro * ''Monitor'' (Polish newspaper), an 18th-century Polish newspaper * ''Concord Monitor'', a daily newspaper in New Hampshire, United States * ''The Monitor'' (Sydney), a biweekly newspaper published between 1826 and 1841 * ''Daily Monitor'', a Ugandan newspaper Television * ''Monitor'' (UK TV programme), a BBC arts programme which aired from 1958 to 19 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |