|
Anna Kournikova (computer Virus)
Anna Kournikova (named Vbs.OnTheFly by its author, and also known as VBS/SST and VBS_Kalamar) was a computer virus that spread worldwide on the Internet in February 2001. The virus program was contained in an email attachment, purportedly an image of tennis player Anna Kournikova. Background The virus was created by 20-year-old Dutch student Jan de Wit, who used the pseudonym "OnTheFly", on 11 February 2001. It was designed to trick email users into clicking to open an email attachment ostensibly appearing to be an image of the professional tennis player Anna Kournikova, but instead hiding a malicious program. The virus arrived in an email with the subject line "Here you have, ;0)" and an attached file entitled AnnaKournikova.jpg.vbs. When opened in Microsoft Outlook, the file did not display a picture of Kournikova, but launched a viral VBScript program that forwarded itself to all contacts in the victim's address book. De Wit created Anna Kournikova in a matter of hours using a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Virus
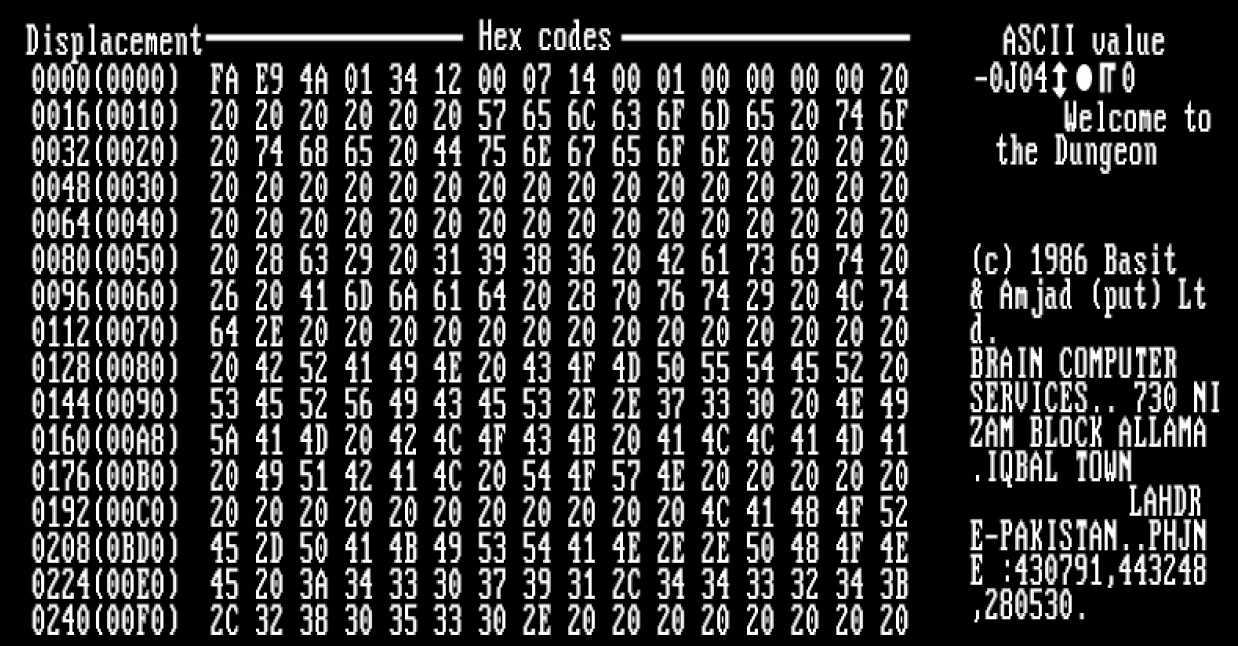
A computer virus is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. A computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks. Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software. Motives for creating viruses can inclu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
International Data Group
International Data Group (IDG, Inc.) is a market intelligence and demand generation company focused on the technology industry. IDG, Inc.’s mission is centered around supporting the technology industry through research, data, marketing technology, and insights that help create and sustain relationships between businesses. IDG, Inc. is wholly owned by Blackstone and is led by Mohamad Ali, who was appointed CEO of the company in 2019. Ali serves on IDG, Inc.’s leadership team along with IDC President Crawford Del Prete, IDG, Inc.’s Chief Financial Officer Donna Marr, and Foundry President Kumaran Ramanathan. IDG, Inc. is headquartered in Needham, MA and is parent company to both International Data Corporation (IDC) and Foundry (formerly IDG Communications). History International Data Group was initially founded as International Data Corporate (IDC) in 1964 by Patrick Joseph McGovern, shortly after he had graduated from the Massachusetts Institute of Technology (MIT). Bas ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hacking In The 2000s
Hacking may refer to: Places * Hacking, an area within Hietzing, Vienna, Austria People * Douglas Hewitt Hacking, 1st Baron Hacking (1884–1950), British Conservative politician * Ian Hacking (born 1936), Canadian philosopher of science * David Hacking, 3rd Baron Hacking (born 1938), British barrister and peer Sports * Hacking (falconry), the practice of raising falcons in captivity then later releasing into the wild * Hacking (rugby), tripping an opposing player * Pleasure riding, horseback riding for purely recreational purposes, also called hacking * Shin-kicking, an English martial art also called hacking Technology * Hacker, a computer expert with advanced technical knowledge ** Hacker culture, activity within the computer programmer subculture * Security hacker, someone who breaches defenses in a computer system ** Cybercrime, which involves security hacking * Phone hacking, gaining unauthorized access to phones * ROM hacking, the process of modifying a video game's pr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Worms
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It will use this machine as a host to scan and infect other computers. When these new worm-invaded computers are controlled, the worm will continue to scan and infect other computers using these computers as hosts, and this behaviour will continue. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on the law of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer. Many worms are designed only to spread, and do not attempt to change the systems they pass through. However, as t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Timeline Of Notable Computer Viruses And Worms
A timeline is a display of a list of events in chronological order. It is typically a graphic design showing a long bar labelled with dates paralleling it, and usually contemporaneous events. Timelines can use any suitable scale representing time, suiting the subject and data; many use a linear scale, in which a unit of distance is equal to a set amount of time. This timescale is dependent on the events in the timeline. A timeline of evolution can be over millions of years, whereas a timeline for the day of the September 11 attacks can take place over minutes, and that of an explosion over milliseconds. While many timelines use a linear timescale—especially where very large or small timespans are relevant -- logarithmic timelines entail a logarithmic scale of time; some "hurry up and wait" chronologies are depicted with zoom lens metaphors. History Time and space, particularly the line, are intertwined concepts in human thought. The line is ubiquitous in clocks in the f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of Convicted Computer Criminals
Convicted computer criminals are people who are caught and convicted of computer crimes such as breaking into computers or computer networks. Computer crime can be broadly defined as criminal activity involving information technology infrastructure, including illegal access (unauthorized access), illegal interception (by technical means of non-public transmissions of computer data to, from or within a computer system), data interference (unauthorized damaging, deletion, deterioration, alteration or suppression of computer data), systems interference (interfering with the functioning of a computer system by inputting, transmitting, damaging, deleting, deteriorating, altering or suppressing computer data), misuse of devices, forgery (or identity theft) and electronic fraud. In the infancy of the hacker subculture and the computer underground, criminal convictions were rare because there was an informal code of ethics that was followed by white hat hackers. Proponents of hackin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Comparison Of Computer Viruses
The compilation of a unified list of computer viruses is made difficult because of naming. To aid the fight against computer viruses and other types of malicious software, many security advisory organizations and developers of anti-virus software compile and publish lists of viruses. When a new virus appears, the rush begins to identify and understand it as well as develop appropriate counter-measures to stop its propagation. Along the way, a name is attached to the virus. As the developers of anti-virus software compete partly based on how quickly they react to the new threat, they usually study and name the viruses independently. By the time the virus is identified, many names denote the same virus. Another source of ambiguity in names is that sometimes a virus initially identified as a completely new virus is found to be a variation of an earlier known virus, in which cases, it is often renamed. For example, the second variation of the Sobig worm was initially called "Palyh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ZDNet
ZDNET is a business technology news website owned and operated by Red Ventures. The brand was founded on April 1, 1991, as a general interest technology portal from Ziff Davis and evolved into an enterprise IT-focused online publication. History Beginnings: 1991 to 1995 ZDNET began as a subscription-based digital service called "ZiffNet" that offered computing information to users of CompuServe. It featured computer industry forums, events, features and searchable archives. Initially, ZiffNet was intended to serve as a common place to find content from all Ziff-Davis print publications. As such, ZiffNet was an expansion on an earlier online service called PCMagNet for readers of PC Magazine. Launched in 1988, PCMagNet in turn was the evolution of Ziff Davis' first electronic publishing venture, a bulletin board, which launched in 1985. On June 20, 1995, Ziff-Davis announced the consolidation of its online information services under a single name, ''ZD Net''. The service had ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Buenos Aires
Buenos Aires ( or ; ), officially the Autonomous City of Buenos Aires ( es, link=no, Ciudad Autónoma de Buenos Aires), is the capital and primate city of Argentina. The city is located on the western shore of the Río de la Plata, on South America's southeastern coast. "Buenos Aires" can be translated as "fair winds" or "good airs", but the former was the meaning intended by the founders in the 16th century, by the use of the original name "Real de Nuestra Señora Santa María del Buen Ayre", named after the Madonna of Bonaria in Sardinia, Italy. Buenos Aires is classified as an alpha global city, according to the Globalization and World Cities Research Network (GaWC) 2020 ranking. The city of Buenos Aires is neither part of Buenos Aires Province nor the Province's capital; rather, it is an autonomous district. In 1880, after decades of political infighting, Buenos Aires was federalized and removed from Buenos Aires Province. The city limits were enlarged to include t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
The Register
''The Register'' is a British technology news website co-founded in 1994 by Mike Magee, John Lettice and Ross Alderson. The online newspaper's masthead sublogo is "''Biting the hand that feeds IT''." Their primary focus is information technology news and opinions. Situation Publishing Ltd is listed as the site's publisher. Drew Cullen is an owner and Linus Birtles is the managing director. Andrew Orlowski was the executive editor before leaving the website in May 2019. History ''The Register'' was founded in London as an email newsletter called ''Chip Connection''. In 1998 ''The Register'' became a daily online news source. Magee left in 2001 to start competing publications ''The Inquirer'', and later the ''IT Examiner'' and ''TechEye''.Walsh, Bob (2007). ''Clear Blogging: How People Blogging Are Changing the World and How You Can Join Them.'' Apress, In 2002, ''The Register'' expanded to have a presence in London and San Francisco, creating ''The Register USA'' at ther ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dutch Guilder
The guilder ( nl, gulden, ) or florin was the currency of the Netherlands from the 15th century until 2002, when it was replaced by the euro. The Dutch name ''gulden'' was a Middle Dutch adjective meaning "golden", and reflects the fact that, when first introduced in 1434, its value was about equal to (i.e., it was on par with) the Italian gold florin. The Dutch guilder was a ''de facto'' reserve currency in Europe in the 17th and 18th centuries. Between 1999 and 2002, the guilder was officially a "national subunit" of the euro. However, physical payments could only be made in guilders, as no euro coins or banknotes were available. The exact exchange rate, still relevant for old contracts and for exchange of the old currency for euros at the central bank, is 2.20371 Dutch guilders for 1 euro. Inverted, this gives 0.453780 euros for 1 guilder. Derived from the Dutch guilder are the Netherlands Antillean guilder (still in use in Curaçao and Sint Maarten) and the Surinamese gui ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Prison
A prison, also known as a jail, gaol (dated, standard English, Australian, and historically in Canada), penitentiary (American English and Canadian English), detention center (or detention centre outside the US), correction center, correctional facility, lock-up, hoosegow or remand center, is a facility in which inmates (or prisoners) are confined against their will and usually denied a variety of freedoms under the authority of the state as punishment for various crimes. Prisons are most commonly used within a criminal justice system: people charged with crimes may be imprisoned until their trial; those pleading or being found guilty of crimes at trial may be sentenced to a specified period of imprisonment. In simplest terms, a prison can also be described as a building in which people are legally held as a punishment for a crime they have committed. Prisons can also be used as a tool of political repression by authoritarian regimes. Their perceived opponents may be ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |